- Cisco Vpn Pre Shared Key
- Cisco Vpn Client Download
- Cisco System Vpn Client Download
- Vpn Pre Shared Key Generator
- Cisco Vpn Pre Shared Key Generator Download
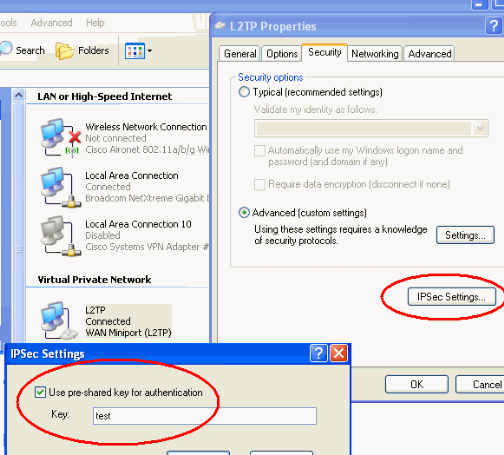
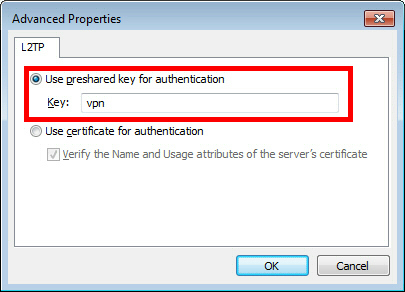
Update the VPN connection pre-shared key, BGP, and IPsec/IKE policy View and update your pre-shared key. Azure S2S VPN connection uses a pre-shared key (secret) to authenticate between your on-premises VPN device and the Azure VPN gateway. Router (config-keyring)# pre-shared-key address 10.2.3.5 key cisco Defines a preshared key to be used for IKE authentication. The address argument specifies the IP address of the remote peer. Step 5: pre-shared-key hostname hostname key key Example: Router (config-keyring)# pre-shared-key hostname mydomain.com key cisco Defines a preshared key.
-->Azure S2S VPN connections provide secure, cross-premises connectivity between customer premises and Azure. This tutorial walks through IPsec S2S VPN connection life cycles such as creating and managing a S2S VPN connection. You learn how to:
- Create an S2S VPN connection
- Update the connection property: pre-shared key, BGP, IPsec/IKE policy
- Add more VPN connections
- Delete a VPN connection
The following diagram shows the topology for this tutorial:
Cisco Vpn Pre Shared Key
Working with Azure Cloud Shell and Azure PowerShell
This article uses PowerShell cmdlets. To run the cmdlets, you can use Azure Cloud Shell. The Azure Cloud Shell is a free interactive shell that you can use to run the steps in this article. It has common Azure tools preinstalled and configured to use with your account.
To open the Cloud Shell, just select Try it from the upper right corner of a code block. You can also launch Cloud Shell in a separate browser tab by going to https://shell.azure.com/powershell. Select Copy to copy the blocks of code, paste it into the Cloud Shell, and press enter to run it.
Requirements
Complete the first tutorial: Create VPN gateway with Azure PowerShell to create the following resources:
- Resource group (TestRG1), virtual network (VNet1), and the GatewaySubnet
- VPN gateway (VNet1GW)
The virtual network parameter values are listed below. Note the additional values for the local network gateway which represent your on-premises network. Change the values below based on your environment and network setup, then copy and paste to set the variables for this tutorial. If your Cloud Shell session times out, or you need to use a different PowerShell window, copy and paste the variables to your new session and continue the tutorial.
Note
If you are using this to make a connection, be sure to change the values to match your on-premises network. If you are just running these steps as a tutorial, you don't need to make changes, but the connection will not work.
The workflow to create an S2S VPN connection is straightforward:
- Create a local network gateway to represent your on-premises network
- Create a connection between your Azure VPN gateway and the local network gateway
Create a local network gateway
A local network gateway represents your on-premises network. You can specify the properties of your on-premises network in the local network gateway, including:
Office 2013 pro plus key generator. So, place a single call on the provided helpline number and get united with the tech-savvy without any worry. There is a technical team who is highly experienced and knowledgeable in technical field. They are ready round the clock to assist you.
- Public IP address of your VPN device
- On-premises address space
- (Optional) BGP attributes (BGP peer IP address and AS number)
Create a local network gateway with the New-AzLocalNetworkGateway command.
Create a S2S VPN connection
Next, create a Site-to-Site VPN connection between your virtual network gateway and your VPN device with the New-AzVirtualNetworkGatewayConnection. Notice that the '-ConnectionType' for Site-to-Site VPN is IPsec.
Add the optional '-EnableBGP $True' property to enable BGP for the connection if you are using BGP. It is disabled by default. Parameter '-ConnectionProtocol' is optional with IKEv2 as default. You can create the connection with IKEv1 protocols by specifying -ConnectionProtocol IKEv1.
Update the VPN connection pre-shared key, BGP, and IPsec/IKE policy
View and update your pre-shared key
Azure S2S VPN connection uses a pre-shared key (secret) to authenticate between your on-premises VPN device and the Azure VPN gateway. You can view and update the pre-shared key for a connection with Get-AzVirtualNetworkGatewayConnectionSharedKey and Set-AzVirtualNetworkGatewayConnectionSharedKey.
Important
The pre-shared key is a string of printable ASCII characters no longer than 128 in length.
This command shows the pre-shared key for the connection:
The output will be 'Azure@!b2C3' following the example above. Use the command below to change the pre-shared key value to 'Azure@!_b2=C3':
Enable BGP on VPN connection
Azure VPN gateway supports BGP dynamic routing protocol. You can enable BGP on each individual connection, depending on whether you are using BGP in your on-premises networks and devices. Specify the following BGP properties before enabling BGP on the connection:
- Azure VPN ASN (Autonomous System Number)
- On-premises local network gateway ASN
- On-premises local network gateway BGP peer IP address
If you have not configured the BGP properties, the following commands add these properties to your VPN gateway and local network gateway: Set-AzVirtualNetworkGateway and Set-AzLocalNetworkGateway.
Cisco Vpn Client Download
Use the following example to configure BGP properties:
Enable BGP with Set-AzVirtualNetworkGatewayConnection.
You can disable BGP by changing the '-EnableBGP' property value to $False. Refer to BGP on Azure VPN gateways for more detailed explanations of BGP on Azure VPN gateways.
Apply a custom IPsec/IKE policy on the connection
You can apply an optional IPsec/IKE policy to specify the exact combination of IPsec/IKE cryptographic algorithms and key strengths on the connection, instead of using the default proposals. The following sample script creates a different IPsec/IKE policy with the following algorithms and parameters:
- IKEv2: AES256, SHA256, DHGroup14
- IPsec: AES128, SHA1, PFS14, SA Lifetime 14,400 seconds & 102,400,000 KB
Refer to IPsec/IKE policy for S2S or VNet-to-VNet connections for a complete list of algorithms and instructions.
Add another S2S VPN connection
Add an additional S2S VPN connection to the same VPN gateway, create another local network gateway, and create a new connection between the new local network gateway and the VPN gateway. Use the following examples, making sure to modify the variables to reflect your own network configuration.
There are now two S2S VPN connections to your Azure VPN gateway.
Delete a S2S VPN connection
Delete a S2S VPN connection with Remove-AzVirtualNetworkGatewayConnection.
Delete the local network gateway if you no longer need it. You cannot delete a local network gateway if there are other connections associated with it.
Clean up resources
If this configuration is part of a prototype, test, or proof-of-concept deployment, you can use the Remove-AzResourceGroup command to remove the resource group, the VPN gateway, and all related resources.
Cisco System Vpn Client Download
Next steps
In this tutorial, you learned about creating and managing S2S VPN connections such as how to:
Vpn Pre Shared Key Generator
- Create an S2S VPN connection
- Update the connection property: pre-shared key, BGP, IPsec/IKE policy
- Add more VPN connections
- Delete a VPN connection
Cisco Vpn Pre Shared Key Generator Download
Advance to the following tutorials to learn about S2S, VNet-to-VNet, and P2S connections. Battlefield 2142 cd key generator keygen v1 2.