Golang RSA Key Generation. @sdorra Why does the code example generate same private and public key while the. @muratsplat If you run it on play.golang.org it. Sign signs an arbitrary length hash (which should be the result of hashing a larger message) using the private key, priv. It returns the signature as a pair of integers. The security of the private key depends on the entropy of rand. Note that FIPS 186-3 section 4.6 specifies that the hash should be truncated to the byte-length of the subgroup. Package crypto/ecdsa GenerateKey generates a public and private key. While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys. This is tool for generate ssh DSA key online and for free.The result of tool generation are ssh dsa private key and ssh dsa public key. Also it's called as 'generate ssh pair'. It will be two text area fileds - the first private key, the second public key. Whats is 'ssh dsa key' and why it is in use?
| // This shows an example of how to generate a SSH RSA Private/Public key pair and save it locally |
| package main |
| import ( |
| 'crypto/rand' |
| 'crypto/rsa' |
| 'crypto/x509' |
| 'encoding/pem' |
| 'golang.org/x/crypto/ssh' |
| 'io/ioutil' |
| 'log' |
| ) |
| func main() { |
| savePrivateFileTo := './id_rsa_test' |
| savePublicFileTo := './id_rsa_test.pub' |
| bitSize := 4096 |
| privateKey, err := generatePrivateKey(bitSize) |
| if err != nil { |
| log.Fatal(err.Error()) |
| } |
| publicKeyBytes, err := generatePublicKey(&privateKey.PublicKey) |
| if err != nil { |
| log.Fatal(err.Error()) |
| } |
| privateKeyBytes := encodePrivateKeyToPEM(privateKey) |
| err = writeKeyToFile(privateKeyBytes, savePrivateFileTo) |
| if err != nil { |
| log.Fatal(err.Error()) |
| } |
| err = writeKeyToFile([]byte(publicKeyBytes), savePublicFileTo) |
| if err != nil { |
| log.Fatal(err.Error()) |
| } |
| } |
| // generatePrivateKey creates a RSA Private Key of specified byte size |
| func generatePrivateKey(bitSize int) (*rsa.PrivateKey, error) { |
| // Private Key generation |
| privateKey, err := rsa.GenerateKey(rand.Reader, bitSize) |
| if err != nil { |
| return nil, err |
| } |
| // Validate Private Key |
| err = privateKey.Validate() |
| if err != nil { |
| return nil, err |
| } |
| log.Println('Private Key generated') |
| return privateKey, nil |
| } |
| // encodePrivateKeyToPEM encodes Private Key from RSA to PEM format |
| func encodePrivateKeyToPEM(privateKey *rsa.PrivateKey) []byte { |
| // Get ASN.1 DER format |
| privDER := x509.MarshalPKCS1PrivateKey(privateKey) |
| // pem.Block |
| privBlock := pem.Block{ |
| Type: 'RSA PRIVATE KEY', |
| Headers: nil, |
| Bytes: privDER, |
| } |
| // Private key in PEM format |
| privatePEM := pem.EncodeToMemory(&privBlock) |
| return privatePEM |
| } |
| // generatePublicKey take a rsa.PublicKey and return bytes suitable for writing to .pub file |
| // returns in the format 'ssh-rsa ..' |
| func generatePublicKey(privatekey *rsa.PublicKey) ([]byte, error) { |
| publicRsaKey, err := ssh.NewPublicKey(privatekey) |
| if err != nil { |
| return nil, err |
| } |
| pubKeyBytes := ssh.MarshalAuthorizedKey(publicRsaKey) |
| log.Println('Public key generated') |
| return pubKeyBytes, nil |
| } |
| // writePemToFile writes keys to a file |
| func writeKeyToFile(keyBytes []byte, saveFileTo string) error { |
| err := ioutil.WriteFile(saveFileTo, keyBytes, 0600) |
| if err != nil { |
| return err |
| } |
| log.Printf('Key saved to: %s', saveFileTo) |
| return nil |
| } |
How to Generate a Public/Private KeyPair for Use With Solaris Secure Shell
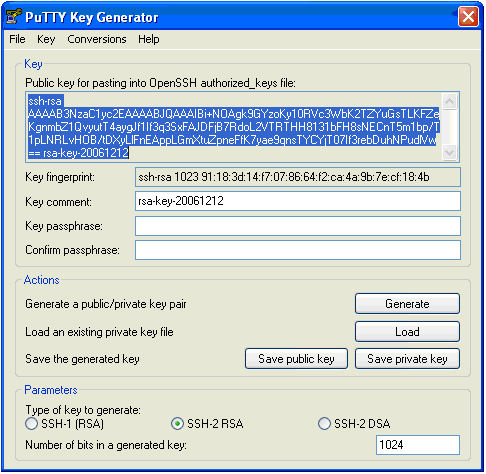
Users must generate a public/private key pair when their site implementshost-based authentication or user public-key authentication. For additionaloptions, see the ssh-keygen(1) manpage.
Before You Begin
Determine from your system administrator if host-based authenticationis configured.
Start the key generation program.
where -t is the type of algorithm, one of rsa, dsa, or rsa1.
Specify the path to the file that will hold the key.
Bydefault, the file name id_rsa, which represents an RSAv2 key, appears in parentheses. You can select this file by pressing the Return key. Or, you can type an alternative file name.
The file name of the public key is created automatically by appendingthe string .pub to the name of the private key file.
Type a passphrase for using your key.
This passphraseis used for encrypting your private key. A null entry is stronglydiscouraged. Note that the passphrase is not displayed when youtype it in.
When answering a question please:. The case is while generating the key I am getting byte length as 16 while the key string length is getting higher than 16. I am doing AES Key Generation in c# and passing the key generated for AES 128 bit Encryption. Where to find encryption key.
Retype the passphrase to confirm it.
Check the results. Alt key ascii code generation.
Check that the path to the keyfile is correct.
At this point, you have created a public/private key pair.
Choose the appropriate option:
If your administrator has configuredhost-based authentication, you might need to copy the local host's publickey to the remote host.
You can now log in to the remote host.For details, see How to Log In to a Remote Host With Solaris Secure Shell.
Type the command on one line with no backslash.
When you are prompted, supply your login password.
If your site uses user authentication with public keys, populateyour authorized_keys file on the remote host.
Copy your public key to the remote host.
Type thecommand on one line with no backslash.
When you are prompted, supply your login password.
Whenthe file is copied, the message “Key copied” is displayed.
(Optional) Reduce the prompting for passphrases.
For a procedure, see How to Reduce Password Prompts in Solaris Secure Shell. For more information, see the ssh-agent(1) and ssh-add(1) man pages.
Example 19–2 Establishing a v1 RSA Key for a User
In the following example, the user cancontact hosts that run v1 of the Solaris Secure Shell protocol. To be authenticated by v1hosts, the user creates a v1 key, then copies the public key portion to theremote host.