Public and private key pairs lie at the core of how is referred to as public key cryptography. Together, they work to secure and authenticate messages. They also lie behind how we authenticate messages at PreVeil.
We often find ourselves explaining the concepts of how these keys work when we talk to prospective clients. So, we thought it would be helpful to discuss what these keys are, what they aren’t and how they work.
The answers below provide a general overview on public and private key pairs rather than an architectural overview of PreVeil. For a detailed understanding of how public-private key pairs work in PreVeil, please review our architectural whitepaper.
- Generate Public Private Key Pair Pem
- Generate Public Private Key Pair Ubuntu
- Generate Public Private Key Pair Git Bash
- Generate Public Private Key Pair Openssl
Generate Public Private Key Pair Pem
Public key vs. private key
- Generating public private key pairs The public and private key are not really keys but rather are really large prime numbers that are mathematically related to one another. Being related in this case means that whatever is encrypted by the public key can only be decrypted by the related private key.
- I am having problem finding a command that would generate a public and private key pair using OpenSSL. Could someone show me some example code of this in action.
The main difference between a public and a private key is their use. The public key , as its name implies, is public and open to anyone in the system. The public key is used to encrypt data.
The private key however is private. It is only ever stored on user’s device. The private key is used to decrypt data.
Public key is used to convert the message to an unreadable form. Private key is used to convert the received message back to the original message. Both these keys help to ensure the security of the exchanged data. A message encrypted with the public key cannot be decrypted without using the corresponding private key.
Generating public private key pairs
The public and private key are not really keys but rather are really large prime numbers that are mathematically related to one another. Being related in this case means that whatever is encrypted by the public key can only be decrypted by the related private key.
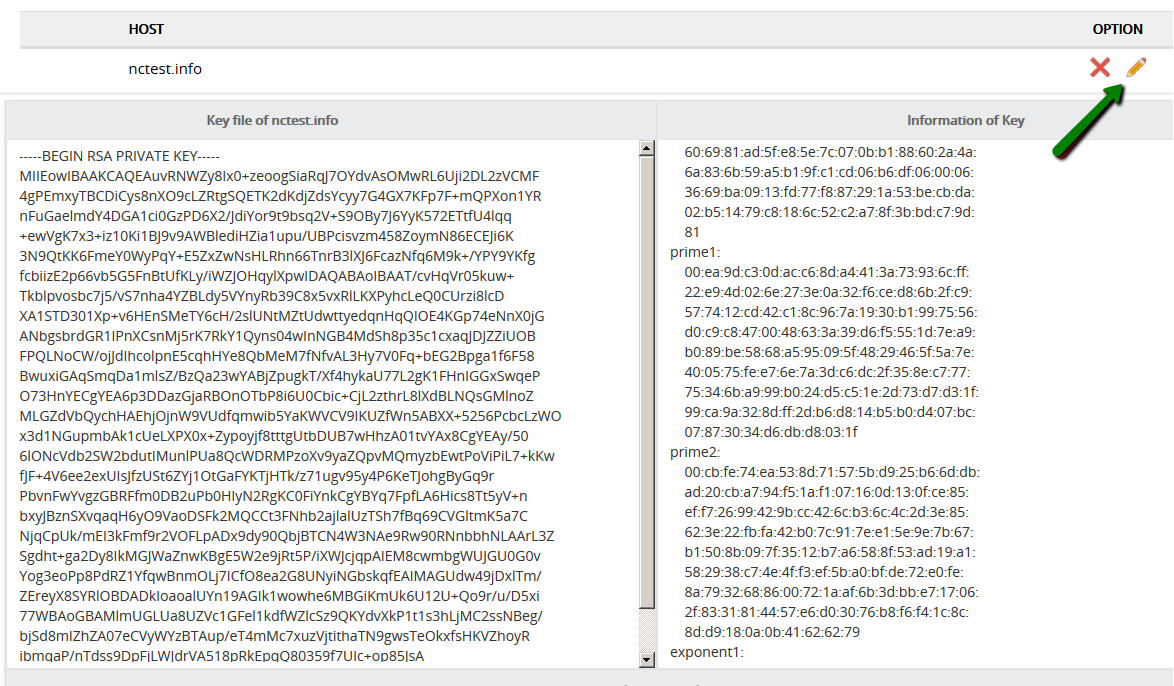
You can generate a public and private RSA key pair like this: openssl genrsa -des3 -out private.pem 2048 That generates a 2048-bit RSA key pair, encrypts them with a password you provide and writes them to a file. You need to next extract the public key file.
A person cannot guess the private key based on knowing the public key. Because of this, a public key can be freely shared. The private key however belongs to only one person.
There are several well-known mathematical algorithms that are used to produce the public and private key. Some well-respected examples of public private key encryption are RSA, DSS (Digital Signature Standard) and various elliptic curve techniques. At PreVeil, we use elliptic-curve cryptography’s Curve-25519 and NIST P-256.
Can a public key decrypt a private key?
In asymmetric cryptography, the public and private key can also be used to create a digital signature. A digital signature assures that the person sending the message is who they claim to be.
Typically, we use the recipient’s public key to encrypt the data and the recipient then uses their private key to decrypt the data. However, using this scheme, there’s no way to authenticate the source of the message. Mike could get a hold of Bob’s public key (since it’s public) and pretend that Bob is the person sending a message to Alice.
To prevent this type of fraud, Bob can sign his message with a digital signature. Digital signatures ensure Mike can’t pretend that he is Bob by using Bob’s public key to send a message to Alice.
To create a digital signature using a public and private key, Bob digitally signs his email to Alice using his private key. When Alice receives the message from Bob, she can verify the digital signature on the message came from Bob by using his public key. As the digital signature uses Bob’s private key, Bob is the only person who could create the signature.
PreVeil’s method for securing messages is a bit more complex than the example provided above. However the example provides a good general overview for how asymmetric encryption works.
How public and private keys work
Public and private keys work together in pairs. As noted above, public keys are disseminated widely and private keys are known only to the owner.
Here’s an example of how the public and private key pair works together:
Bob wants to send Alice an encrypted email. To do this, Bob takes Alice’s public key and encrypts his message to her. Then, when Alice receives the message, she takes the private key that is known only to her in order to decrypt the message from Bob and reads it.
Although the companies owning the server might try to read the message, they will be unable to because they lack the private key to decrypt the message. Only Alice will be able to decrypt the message as she is the only one with the private key.
When Alice wants to reply, she simply repeats the process, encrypting her message to Bob using Bob’s public key.
Examples of public private key encryption.
Many protocols like SSH, OpenPGP, S/MIME, and SSL/TLS rely on asymmetric cryptography for encryption and digital signatures. It is also used in software programs, such as browsers, to establish secure connections over an insecure network like the internet.
PreVeil is one example platform that uses public and private keys to encrypt data and create digital signatures. Other well-known applications that use public and private keys to secure messages are WhatsApp and Signal.
Generate Public Private Key Pair Ubuntu
Business benefits of public private key encryption
By using a public and private key for encryption and decryption, recipients can be confident that the data is what the sender says it is. The recipient is assured of the confidentiality, integrity and authenticity of the data.
Confidentiality is ensured because the content that is secured with the public key can only be decrypted with the private key. This ensures that only the intended recipient can ever review the contents
Integrity is ensured because part of the decryption process requires checking that the received message matches the sent message. This ensures that the message has not been changed in between.
Authenticity is ensured because each message sent by Alice to Bob is also signed by Alice’s private key. The only way to decrypt Alice’s private key is with her public key, which Bob can access. By signing the message with her private key, Alice ensures the authenticity of the message and shows that it really did come from her.
Conclusion
Interested in reading more about public private keys? Look at our articles on:
End-to-end encryption
Email encryption
Or watch our video on how public and private keys secure enterprise email:
Several tools exist to generate SSH public/private key pairs. The following sections show how to generate an SSH key pair on UNIX, UNIX-like and Windows platforms.
Generating an SSH Key Pair on UNIX and UNIX-Like Platforms Using the ssh-keygen Utility
UNIX and UNIX-like platforms (including Solaris and Linux) include the ssh-keygen utility to generate SSH key pairs.

Generate Public Private Key Pair Git Bash
- Navigate to your home directory:
- Run the ssh-keygen utility, providing as
filenameyour choice of file name for the private key:The ssh-keygen utility prompts you for a passphrase for the private key.
- Enter a passphrase for the private key, or press Enter to create a private key without a passphrase:
Note:
While a passphrase is not required, you should specify one as a security measure to protect the private key from unauthorized use. When you specify a passphrase, a user must enter the passphrase every time the private key is used.
The ssh-keygen utility prompts you to enter the passphrase again.
- Enter the passphrase again, or press Enter again to continue creating a private key without a passphrase:
- The ssh-keygen utility displays a message indicating that the private key has been saved as
filenameand the public key has been saved asfilename.pub. It also displays information about the key fingerprint and randomart image.
Generating an SSH Key Pair on Windows Using the PuTTYgen Program
The PuTTYgen program is part of PuTTY, an open source networking client for the Windows platform.
 Sep 12, 2017 You are prompted for a pass-phrase for the key, and for information about your CA, such as your location, organization name, and so on. Use a strong pass-phrase to secure your private key, and type the required information for the CA. The private key and root certificate are created. Generate the CA private key. Generate the CA self-signed certificate. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.' , the field will be left blank. Nov 29, 2017 For security reasons, the Certificate Authority doesn’t keep that private key. If you try to export a certificate from the Issued folder on the CA, you can only export (Copy To File) as a.cer file, which won’t include the private key. Apr 09, 2020 CA Key and Certificate Creation Generate a CA private key file using a utility (OpenSSL, cfssl etc). Create the CA root certificate using the CA private key. The first of which they should already have (the self-signed CA certificate). The second contains the public key that you want verified, and is signed with the CA certificate (using the associated CA private key). The validity of the second certificate is tested using the public key in the CA certificate. Private keys are always kept private.
Sep 12, 2017 You are prompted for a pass-phrase for the key, and for information about your CA, such as your location, organization name, and so on. Use a strong pass-phrase to secure your private key, and type the required information for the CA. The private key and root certificate are created. Generate the CA private key. Generate the CA self-signed certificate. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.' , the field will be left blank. Nov 29, 2017 For security reasons, the Certificate Authority doesn’t keep that private key. If you try to export a certificate from the Issued folder on the CA, you can only export (Copy To File) as a.cer file, which won’t include the private key. Apr 09, 2020 CA Key and Certificate Creation Generate a CA private key file using a utility (OpenSSL, cfssl etc). Create the CA root certificate using the CA private key. The first of which they should already have (the self-signed CA certificate). The second contains the public key that you want verified, and is signed with the CA certificate (using the associated CA private key). The validity of the second certificate is tested using the public key in the CA certificate. Private keys are always kept private.

Generate Public Private Key Pair Openssl
- Download and install PuTTY or PuTTYgen.
To download PuTTY or PuTTYgen, go to http://www.putty.org/ and click the You can download PuTTY here link.
- Run the PuTTYgen program.
- Set the Type of key to generate option to SSH-2 RSA.
- In the Number of bits in a generated key box, enter 2048.
- Click Generate to generate a public/private key pair.
As the key is being generated, move the mouse around the blank area as directed.
- (Optional) Enter a passphrase for the private key in the Key passphrase box and reenter it in the Confirm passphrase box.
Note:
While a passphrase is not required, you should specify one as a security measure to protect the private key from unauthorized use. When you specify a passphrase, a user must enter the passphrase every time the private key is used.
- Click Save private key to save the private key to a file. To adhere to file-naming conventions, you should give the private key file an extension of
.ppk(PuTTY private key).Note:
The.ppkfile extension indicates that the private key is in PuTTY's proprietary format. You must use a key of this format when using PuTTY as your SSH client. It cannot be used with other SSH client tools. Refer to the PuTTY documentation to convert a private key in this format to a different format. - Select all of the characters in the Public key for pasting into OpenSSH authorized_keys file box.
Make sure you select all the characters, not just the ones you can see in the narrow window. If a scroll bar is next to the characters, you aren't seeing all the characters.
- Right-click somewhere in the selected text and select Copy from the menu.
- Open a text editor and paste the characters, just as you copied them. Start at the first character in the text editor, and do not insert any line breaks.
- Save the text file in the same folder where you saved the private key, using the
.pubextension to indicate that the file contains a public key. - If you or others are going to use an SSH client that requires the OpenSSH format for private keys (such as the
sshutility on Linux), export the private key:- On the Conversions menu, choose Export OpenSSH key.
- Save the private key in OpenSSH format in the same folder where you saved the private key in
.ppkformat, using an extension such as.opensshto indicate the file's content.