<<TableOfContents: execution failed [Argument 'maxdepth' must be an integer value, not '[1]'] (see also the log)>>
- Centos Generate New Ssh Host Keys
- Ssh Keygen Centos
- How To Ssh Into Centos
- Generate Ssh Host Keys Centos 6
- Centos Ssh Key Setup
- Generate Ssh Host Keys Centos 1
- Centos Ssh Setup
- Nov 26, 2018 How to use SSH keys with Windows on Azure.; 6 minutes to read +2; In this article. This article describes ways to generate and use secure shell (SSH) keys on a Windows computer to create and connect to a Linux virtual machine (VM) in Azure.
- How to regenerate new ssh server keys This is an unusual topic since most distribution create these keys for you during the installation of the OpenSSH server package. But it may be useful to be able generate new server keys from time to time, this happen to me when I duplicate Virtual Private Server which contains an installed ssh package.
OpenSSH (or Secure SHell) has become a de facto standard for remote access replacing the telnet protocol. SSH has made protocols such as telnet redundant due, in most part, to the fact that the connection is encrypted and passwords are no longer sent in plain text for all to see.
However, a default installation of ssh isn't perfect, and when running an ssh server there are a few simple steps that can dramatically harden an installation.
When you install a fresh system, then at the start of the ssh service, it generates the host keys for your system which later on used for authentication. But if due to some reason you need to generate the host keys, then the process is explained below.
1. Use Strong Passwords/Usernames
One of the first things you'll notice if you have ssh running and exposed to the outside world is that you'll probably log attempts by hackers to guess your username/password. Typically a hacker will scan for port 22 (the default port on which ssh listens) to find machines with ssh running, and then attempt a brute-force attack against it. With strong passwords in place, hopefully any attack will be logged and noticed before it can succeed.
Hopefully you already use strong passwords, but if you are not then try to choose passwords that contains:
Then you don’t worried about it. Windows 7 home premium product key generator free download.
- Minimum of 8 characters
- Mix of upper and lower case letters
- Mix of letters and numbers
- Non alphanumeric characters (e.g. special characters such as ! ' £ $ % ^ etc)
The benefits of strong passwords aren't specific to ssh, but have an impact on all aspects of systems security. Further information on passwords can be found in the CentOS documentation:
http://www.centos.org/docs/4/html/rhel-sg-en-4/s1-wstation-pass.html
If you absolutely can't prevent your users choosing weak passwords, then consider using randomly generated or difficult to guess usernames for your user accounts. If the bad guys can't guess the username then they can't brute force the password. However, this is still security through obscurity and be aware of information leakage of usernames from things such as email sent from user accounts.
2. Disable Root Logins
SSH server settings are stored in the /etc/ssh/sshd_config file. To disable root logins, make sure you have the following entry:
and restart the sshd service:
If you need root access, login as a normal user and use the su command.
3. Limit User Logins
SSH logins can be limited to only certain users who need remote access. If you have many user accounts on the system then it makes sense to limit remote access to only those that really need it thus limiting the impact of a casual user having a weak password. Add an AllowUsers line followed by a space separated list of usernames to /etc/ssh/sshd_config For example:
and restart the sshd service.
4. Disable Protocol 1
SSH has two protocols it may use, protocol 1 and protocol 2. The older protocol 1 is less secure and should be disabled unless you know that you specifically require it. Look for the following line in the /etc/ssh/sshd_config file, uncomment it and amend as shown:
and restart the sshd service.
5. Use a Non-Standard Port
By default, ssh listens for incoming connections on port 22. For a hacker to determine ssh is running on your machine, he'll most likely scan port 22 to determine this. An effective method is to run ssh on a non-standard port. Any unused port will do, although one above 1024 is preferable. Many people choose 2222 as an alternative port (as it's easy to remember), just as 8080 is often known as the alternative HTTP port. For this very reason, it's probably not the best choice, as any hacker scanning port 22 will likely also be scanning port 2222 just for good measure. It's better to pick some random high port that's not used for any known services. To make the change, add a line like this to your /etc/ssh/sshd_config file:
and restart the sshd service. Don't forget to then make any necessary changes to port forwarding in your router and any applicable firewall rules. For example on CentOS 7 (and higher) you can change firewalld's ssh service by making a duplicate of its service file in /etc/firewalld/ and changing its port line:
Then change the port line in /etc/firewalld/services/ssh-custom.xml so the port is the same as in the ssh config file:
Lastly, remove the ssh service, add the ssh-custom service, and reload firewalld for the change to take effect:
Or on CentOS 6, add an iptable rule to open the new ssh port:
Don't forget to close the old port as well.
On CentOS 6 and above you should also update selinux, labeling the chosen port correctly, otherwise sshd will be prevented from accessing it. For example:
Because ssh is no longer listening for connections on the standard port, you will need to tell your client what port to connect on. Using the ssh client from the command line, we may specify the port using the -p switch:
or if you are using the fish protocol in konqueror, for example:
If you are thinking that this sounds like a pain having to specify the port each time you connect, simply add an entry specifying the port in your local ~/.ssh/config file:
And the file: ~/.ssh/config must have the following permissions:
6. Filter SSH at the Firewall
If you only need remote access from one IP address (say from work to your home server), then consider filtering connections at your firewall by either adding a firewall rule on your router or in iptables to limit access on port 22 to only that specific IP address. For example, in iptables this could be achieved with the following type of rule for iptables (CentOS 6):
or using firwalld (CentOS 7) use rich-rules to allow ssh on only a specific port. The source address may be a single address or a base address with a bitmask:
SSH also natively supports TCP wrappers and access to the ssh service may be similarly controlled using hosts.allow and hosts.deny.
If you are unable to limit source IP addresses, and must open the ssh port globally, then iptables can still help prevent brute-force attacks by logging and blocking repeated attempts to login from the same IP address. For example, with iptables
The first rule records the IP address of each new attempt to access port 22 using the recent module. The second rule checks to see if that IP address has attempted to connect 4 or more times within the last 60 seconds, and if not then the packet is accepted. Note this rule would require a default policy of DROP on the input chain.
Don't forget to change the port as appropriate if you are running ssh on a non-standard port. Where possible, filtering at the firewall is an extremely effective method of securing access to an ssh server.
For systems using the FirewallD service (CentOS 7 or higher), use firewall-cmd:
The first command removes the more permissive service rule, the second instates a rule to accept only 4 connections in a minute and log all connections.
Centos Generate New Ssh Host Keys
7. Use Public/Private Keys for Authentication
Using encrypted keys for authentication offers two main benefits. Firstly, it is convenient as you no longer need to enter a password (unless you encrypt your keys with password protection) if you use public/private keys. Secondly, once public/private key pair authentication has been set up on the server, you can disable password authentication completely meaning that without an authorized key you can't gain access - so no more password cracking attempts.
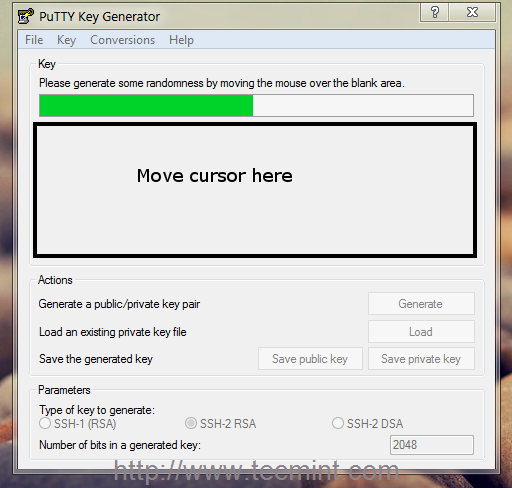
It's a relatively simple process to create a public/private key pair and install them for use on your ssh server.
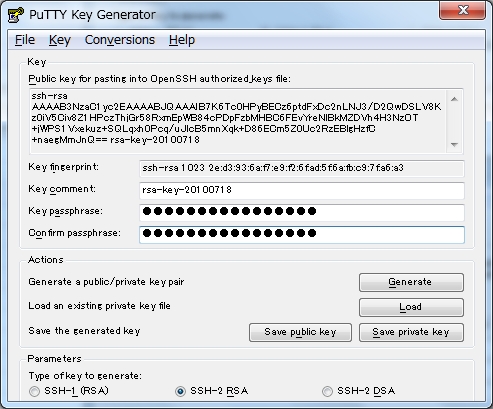
First, create a public/private key pair on the client that you will use to connect to the server (you will need to do this from each client machine from which you connect):
This will create two files in your (hidden) ~/.ssh directory called: id_rsa and id_rsa.pub The first: id_rsa is your private key and the other: id_rsa.pub is your public key.
If you don't want to still be asked for a passphrase (which is basically a password to unlock a given public key) each time you connect, just press enter when asked for a passphrase when creating the key pair. It is up to you to decide whether or not you should add the passphrase protective encryption to your key when you create it. If you don't passphrase protect your key, then anyone gaining access to your local machine will automatically have ssh access to the remote server. Also, root on the local machine has access to your keys although one assumes that if you can't trust root (or root is compromised) then you're in real trouble. Encrypting the key adds additional security at the expense of eliminating the need for entering a password for the ssh server only to be replaced with entering a passphrase for the use of the key. This may be further simplified by the use of the ssh_agent program
Now set permissions on your private key:
Copy the public key (id_rsa.pub) to the server and install it to the authorized_keys list:
Note: once you've imported the public key, you can delete it from the server.
and finally set file permissions on the server:
The above permissions are required if StrictModes is set to yes in /etc/ssh/sshd_config (the default).
Ensure the correct SELinux contexts are set:
Now when you login to the server you won't be prompted for a password (unless you entered a passphrase when you created your key pair). By default, ssh will first try to authenticate using keys. If no keys are found or authentication fails, then ssh will fall back to conventional password authentication.
Once you've checked you can successfully login to the server using your public/private key pair, you can disable password authentication completely by adding the following setting to your /etc/ssh/sshd_config file:
8. Frequently Asked Question (FAQ)
Q: CentOS uses version X of OpenSSH and the latest version is version Y. Version X contained a serious security flaw, should I upgrade?
A: No. The Upstream Vendor has a policy of backporting security patches from the latest releases into the current distribution version. As long as you have the latest updates applied for your CentOS distribution you are fully patched. See here for further details of backporting security patches:
http://www.redhat.com/advice/speaks_backport.html
Q: How to I get ssh to allow passwordless key based authentication between machines that share users' home directories by NFS?
A: SElinux blocks root access to NFS shared directories and files that are not world readable by default and so sshd can't read users' key files in ~/.ssh. To enable access, change the setting of use_nfs_home_dirs by running the following command as the superuser:
https://www.centos.org/forums/viewtopic.php?t=49194
9. Links
http://www.centos.org/docs/5/html/Deployment_Guide-en-US/ch-openssh.html
http://www.dragonresearchgroup.org/insight/sshpwauth-tac.html
Introduction
Establishing an SSH (Secure Shell) connection is essential to log in and effectively manage a remote server. Encrypted keys are a set of access credentials used to establish a secure connection.
This guide will walk you how to generate SSH keys on Ubuntu 18.04. We will also cover setting up SSH key-based authentication to connect to a remote server without requiring a password.
- A server running Ubuntu 18.04
- A user account with sudo privileges
- Access to a terminal window / command line (Ctrl-Alt-T)
If you are already running an Ubuntu 18.04 server, you can skip this step. If you are configuring your server for the first time, you may not have SSH installed.
1. Start by installing the tasksel package:
The system will first ask for confirmation before proceeding:
2. Next, use tasksel to install the ssh-server:
Every IP address has its own account and it is provided with free credits that can be used topay for Online Domain Tools services. This is why we call them Daily Credits.Accounts of registered users have higher Daily Credits amounts and can even increase them by purchasing subscriptions.Besides Daily Credits, all accounts, including IP address accounts of anonymous users, have their creditWallet. Moreover, credit balance is reset every day. Wallet credits are not reset on a daily basis, but they are only spent when a user has not enough Daily Credits. Key generation failed encrypt_aes informix data.
3. Load the SSH server service, and set it to launch at boot:
On your client system – the one you’re using to connect to the server – you need to create a pair of key codes.
To generate a pair of SSH key codes, enter the commands:
This will create a hidden directory to store your SSH keys, and modify the permissions for that directory. The ssh-keygen command creates a 2048-bit RSA key pair.
For extra security, use RSA4096:
If you’ve already generated a key pair, this will prompt to overwrite them, and those old keys will not work anymore.
The system will ask you to create a passphrase as an added layer of security. Input a memorable passphrase, and press Enter.
Ssh Keygen Centos
This process creates two keys. One is a public key, which you can hand out to anyone – in this case, you’ll save it to the server. The other one is a private key, which you will need to keep secure. The secure private key ensures that you are the only person who can encrypt the data that is decrypted by the public key.
Step 2- Copy Public Key to the Ubuntu Server
First, get the IP address of the Ubuntu server you want to connect to.
In a terminal window, enter:
The system’s IP address is listed in the second entry:
On the client system, use the ssh-copy-id command to copy the identity information to the Ubuntu server:
Replace server_IP with the actual IP address of your server.
If this is the first time you’re connecting to the server, you may see a message that the authenticity of the host cannot be established:
Type yes and press Enter.
The system will check your client system for the id_rsa.pub key that was previously generated. Then it will prompt you to enter the password for the server user account. Type it in (the system won’t display the password), and press Enter.
How To Ssh Into Centos
The system will copy the contents of the ~/.ssh/id_rsa.pub from the client system into the ~/.ssh/authorized_keys directory of the server system.
The system should display:
If your system does not have the ssh-copy-id command, you can copy the key manually over the SSH.
Use the following command:
To log in to a remote server, input the command:
The system should not ask for a password as it is negotiating a secure connection using the SSH keys. If you used a security passphrase, you would be prompted to enter it. After you do so, you are logged in.
If this is the first time you’ve logged into the server, you may see a message similar to the one in part two. It will ask if you are sure you want to connect – type yes and press Enter.
Step 4- Disable Password Authentication
This step creates an added layer of security. If you’re the only person logging into the server, you can disable the password. The server will only accept a login with your private key to match the stored public key.
Edit the sshd_config file:
Search the file and find the PasswordAuthentication option.
Edit the file and change the value to no:
Save the file and exit, then restart the SSH service:
Verify that SSH is still working, before ending the session:
Generate Ssh Host Keys Centos 6
If everything works, you can close out and resume work normally.
By following the instructions in this tutorial, you have setup SSH-key-based authentication on an Ubuntu 18.04 server.
The connection is now highly secure as it uses a set of unique, encrypted SSH keys.
Centos Ssh Key Setup
Next you should also read
Learn how to set up SSH key authentication on CentOS to safely communicate with remote servers. Create the…
When establishing a remote connection between a client and a server, a primary concern is ensuring a secure…
Generate Ssh Host Keys Centos 1
Nginx is an open-source server utility designed to work as a reverse proxy, intercepting client requests and…
Centos Ssh Setup
In this tutorial, Find out How To Use SSH to Connect to a Remote Server in Linux or Windows. Get started with…