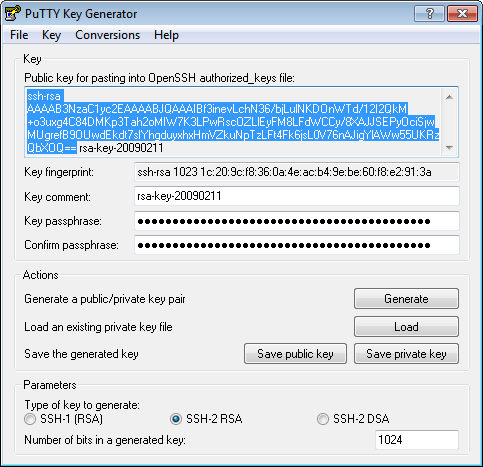
Aug 07, 2019 How do I set up SSH keys on a Linux or Unix based systems? In SSH for Linux/Unix, how do I set up public key authentication? This page explains a public key and shows you how to set up SSH keys on a Linux or Unix-like server. I am assuming that you are using Linux or Unix-like server and client with the following software. Aug 30, 2019 The -i option specifies the key to use and works the same with all of the SSH client utilities, including the ssh, ssh-copy-id, and scp commands: $ ssh -i /.ssh/idsomehubs user@host This option can be given muliple times to limit which keys to try, if you know it is one of a handful of keys, but I usually only need to specify the exact key. Red Hat Enterprise Linux (RHEL) 6.3; Issue. SSH Keys generated by Putty do not work with openssh in Red Hat Enterprise Linux; Resolution. To make it working convert the keys generated by Open-ssh to putty's format: First generate keys on RHEL: # ssh-keygen -t rsa Then put public key into authorizedkeys file: # cat publickey /.ssh.
Additionally, you must copy the generated private key called idrsa to each of the CDS server instances. Copy the files to the /.ssh/ directory of each CDS instance. Note that the permissions for the /.ssh/ directory should be set 700 to allow automated authentication and connection to the CDS instances. Adding an SSH Key Paste in the public key for the host, and click Set. Setting an SSH Key The SSH public keys area now shows the new key. Clicking Show/Set key opens the submitted key. To upload multiple keys, click the Add link below the list of public keys, and upload the other keys.
recently read that SSH keys provide a secure way of logging into a Linux and Unix-based server. How do I set up SSH keys on a Linux or Unix based systems? In SSH for Linux/Unix, how do I set up public key authentication?This page explains a public key and shows you how to set up SSH keys on a Linux or Unix-like server. I am assuming that you are using Linux or Unix-like server and client with the following software:
- OpenSSH SSHD server
- OpenSSH ssh client and friends on Linux (Ubuntu, Debian, {Free,Open,Net}BSD, RHEL, CentOS, MacOS/OSX, AIX, HP-UX and co).
What is a public key authentication?
OpenSSH server supports various authentication schema. The two most popular are as follows:
- Passwords based authentication
- Public key based authentication. It is an alternative security method to using passwords. This method is recommended on a VPS, cloud, dedicated or even home based server.
How to set up SSH keys
Steps to setup secure ssh keys:
- Create the ssh key pair using ssh-keygen command.
- Copy and install the public ssh key using ssh-copy-id command on a Linux or Unix server.
- Add yourself to sudo or wheel group admin account.
- Disable the password login for root account.
- Test your password less ssh keys login using ssh user@server-name command.
Let us see all steps in details.
How do I set up public key authentication?
You must generate both a public and a private key pair. For example:
Where,
- server1.cyberciti.biz – You store your public key on the remote hosts and you have an accounts on this Linux/Unix based server.
- client1.cyberciti.biz – Your private key stays on the desktop/laptop/ computer (or local server) you use to connect to server1.cyberciti.biz server. Do not share or give your private file to anyone.
In public key based method you can log into remote hosts and server, and transfer files to them, without using your account passwords. Feel free to replace server1.cyberciti.biz and client1.cyberciti.biz names with your actual setup. Enough talk, let’s set up public key authentication. Open the Terminal and type following commands if .ssh directory does not exists:
1: Create the key pair
On the computer (such as client1.cyberciti.biz), generate a key pair for the protocol.
Sample outputs:
You need to set the Key Pair location and name. I recommend you use the default location if you do not yet have another key there, for example: $HOME/.ssh/id_rsa. You will be prompted to supply a passphrase (password) for your private key. I suggest that you setup a passphrase when prompted. You should see two new files in $HOME/.ssh/ directory:
- $HOME/.ssh/id_rsa– contains your private key.
- $HOME/.ssh/id_rsa.pub – contain your public key.
Optional syntax for advance users
The following syntax specifies the 4096 of bits in the RSA key to creation (default 2048):$ ssh-keygen -t rsa -b 4096 -f ~/.ssh/vps-cloud.web-server.key -C 'My web-server key'
Where,
Generate Ssh Key Windows
- -t rsa : Specifies the type of key to create. The possible values are “rsa1” for protocol version 1 and “dsa”, “ecdsa”, “ed25519”, or “rsa” for protocol version 2.
- -b 4096 : Specifies the number of bits in the key to create
- -f ~/.ssh/vps-cloud.web-server.key : Specifies the filename of the key file.
- -C 'My web-server key' : Set a new comment.
2: Install the public key in remote server
Use scp or ssh-copy-id command to copy your public key file (e.g., $HOME/.ssh/id_rsa.pub) to your account on the remote server/host (e.g., [email protected]). To do so, enter the following command on your client1.cyberciti.biz:
OR just copy the public key in remote server as authorized_keys in ~/.ssh/ directory:
A note about appending the public key in remote server
On some system ssh-copy-id command may not be installed, so use the following commands (when prompted provide the password for remote user account called vivek) to install and append the public key:
3: Test it (type command on client1.cyberciti.biz)
The syntax is as follows for the ssh command:
Or copy a text file called foo.txt:
You will be prompted for a passphrase. To get rid of passphrase whenever you log in the remote host, try ssh-agent and ssh-add commands.
What are ssh-agent and ssh-add, and how do I use them?
To get rid of a passphrase for the current session, add a passphrase to ssh-agent and you will not be prompted for it when using ssh or scp/sftp/rsync to connect to hosts with your public key. The syntax is as follows:
Type the ssh-add command to prompt the user for a private key passphrase and adds it to the list maintained by ssh-agent command:
Enter your private key passphrase. Now try again to log into [email protected] and you will not be prompted for a password:
One can list public key parameters of all identities with the -L option:ssh-add -L
Deleting all private keys from the ssh-agent can be done with the -D option as follows:ssh-add -D
When you log out kill the ssh agent, run:kill $SSH_AGENT_PID
You can also add something like the below to your shell startup to kill ssh-agent at logout:trap 'kill $SSH_AGENT_PID' 0
4: Disable the password based login on a server
Login to your server, type:
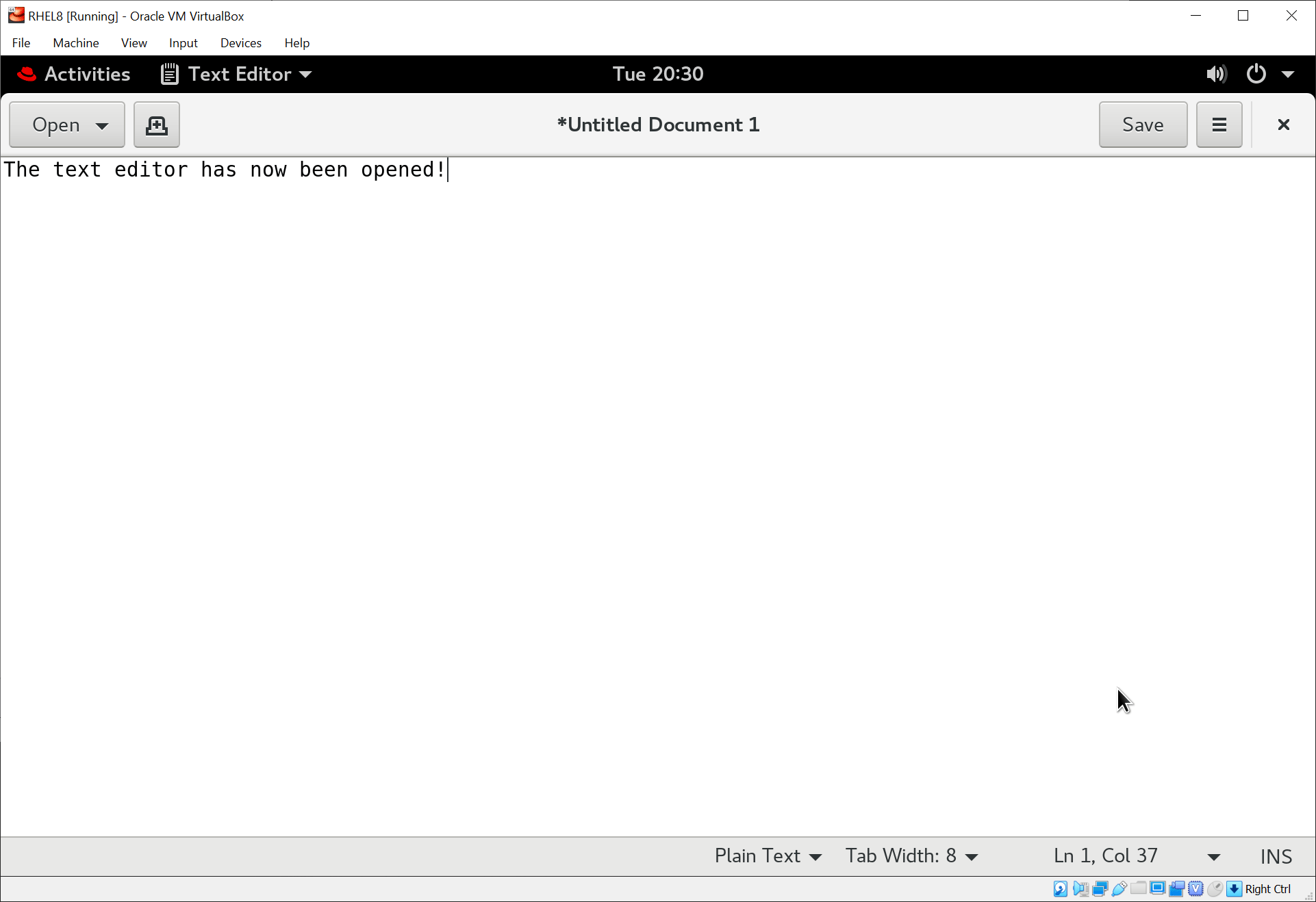
Edit /etc/ssh/sshd_config on server1.cyberciti.biz using a text editor such as nano or vim:
Jul 21, 2016 DELTA FORCE 4 DELTA FORCE 4 pc game serial key DELTA FORCE 4 pc game key DELTA FORCE 4 game key DELTA FORCE 4 game serial key delta force delta force 4 delta force 4. Download now the serial number for Delta Force task force dagger. All serial numbers are genuine and you can find more results in our database for Delta software. Updates are issued periodically and new results might be added for this applications from our community. Delta force task force dagger cd key generator. Jun 27, 2002 For Delta Force: Task Force Dagger on the PC, GameFAQs has 6 cheat codes and secrets.
Warning: Make sure you add yourself to sudoers files. Otherwise you will not able to login as root later on. See “How To Add, Delete, and Grant Sudo Privileges to Users on a FreeBSD Server” for more info.
$ sudo vim /etc/ssh/sshd_config
OR directly jump to PermitRootLogin line using a vim text editor:$ sudo vim +/PermitRootLogin /etc/ssh/sshd_config
Find PermitRootLogin and set it as follows:
Save and close the file. I am going to add a user named vivek to sudoers on Ubuntu Linux:# adduser vivek
Finally, reload/restart the sshd server, type command as per your Linux/Unix version:
5: How to add or replace a passphrase for an existing private key?
To to change your passphrase type the following command:ssh-keygen -p
6: How do I backup an existing private/public key?
Just copy files to your backup server or external USB pen/hard drive:
How do I protect my ssh keys?
- Always use a strong passphrase.
- Do not share your private keys anywhere online or store in insecure cloud storage.
- Restrict privileges of the account.
How do I create and setup an OpenSSH config file to create shortcuts for servers I frequently access?
See how to create and use an OpenSSH ssh_config file for more info.
Conclusion
This page explained how to set up ssh keys for authentication purposes. For more info see the following resources:
- Man pages – ssh-keygen(1)
- OpenSSH project homepage here.
And, there you have it, ssh set up with public key based authentication for Linux or Unix-like systems.
ADVERTISEMENTS
If you interact regularly with SSH commands and remote hosts, you may find that using a key pair instead of passwords can be convenient. Instead of the remote system prompting for a password with each connection, authentication can be automatically negotiated using a public and private key pair.
The private key remains secure on your own workstation, and the public key gets placed in a specific location on each remote system that you access. Your private key may be secured locally with a passphrase. A local caching program such as ssh-agent or gnome-keyring allows you to enter that passphrase periodically, instead of each time you use the key to access a remote system.
Generating a key pair and propagating the public key
Generating your key pair and propagating your public key is simpler than it sounds. Let’s walk through it.
Dec 23, 2013 Tune up utilities 2014 Full version free download+ Crack - Duration. 10 Easily Windows Product, Serial Key Generator. AVG PC TUNEUP 2017 Product key - Duration: 9:40. Download now the serial number for TuneUp Utilities 2014 Serial keys. All serial numbers are genuine and you can find more results in our database for TuneUp software. Updates are issued periodically and new results might be added for this applications from our community. Free avg pc tuneup 2014 product key generator. AVG Tuneup 2014 product key generator download free utilities: AVG is most old name in the history of pc and system security.”AVG tuneup utilities” is also a well known name in pc security department.You can enjoy full tuneup utilities setup by AVG Tuneup 2014 product key generator.Generate product keys for AVG tuneup utilities 2014 as much as you desired. Nov 08, 2013 TuneUp Utilities from AVG is a system application, which allows you to optimize the performance of you computer. It helps you to customize your system to fulfill your need. It is one of the best system optimizing tool available now a days. You can clean your system by removing unwanted and temporary files which slows down your pc. Dec 26, 2013 AVG PC TUNE-UP 2014: CMI4A-VHVH9-6JQQP-AHUTQ-I4EP7-6IOYS. All Trusted and 100% PC TuneUp & TuneUp Utilities Software Free Download Link AVG PC TuneUp & TuneUp Utilities 2014 100% Guaranty for Work. Please could someone send me the product key for AVG PC TuneUp 2014, thanks [email protected]. Reply Delete.
Generating the key
The minimum effort to generate a key pair involves running the ssh-keygen command, and choosing the defaults at all the prompts:
The default location to store the keys is in the ~/.ssh directory, which will be created if it does not exist:
Allowing this command to create the directory also ensures that the owner and permissions are set correctly. Some applications will not use keys if the permissions to the private key are too open.
The file ending in .pub is the public key that needs to be transferred to the remote systems. It is a file containing a single line: The protocol, the key, and an email used as an identifier. Options for the ssh-keygen command allow you to specify a different identifier:
After generating the key pair, the ssh-keygen command also displays the fingerprint and randomart image that are unique to this key. This information can be shared with other people who may need to verify your public key.
Later you can view these with:
The -l option lists the fingerprint, and the -v option adds the ASCII art.
Propagating the public key to a remote system
If password authentication is currently enabled, then the easiest way to transfer the public key to the remote host is with the ssh-copy-id command. If you used the default name for the key all you need to specify is the remote user and host:
Following the instructions from the output, verify that you can connect using the key pair. If you implemented a passphrase, you will be prompted for the passphrase to use the private key:
Examine the resulting authorized key file. This is where the public key was appended. If the directory or file did not exist, then it was (or they were) created with the correct ownership and permissions. Each line is a single authorized public key:
To revoke access for this key pair, remove the line for the public key.
There are many other options that can be added to this line in the authorized key file to control access. These options are usually used by administrators placing the public keys on a system with restrictions. These restrictions may include where the connection may originate, what command(s) may be run, and even a date indicating when to stop accepting this key. These and more options are listed in the sshd man page.
Changing the passphrase
If you need to change a passphrase on your private key or if you initially set an empty passphrase and want that protection at a later time, use the ssh-keygen command with the -p option:
Generate Ssh Key Linux Azure
You can add additional options to specify the key (-f), and the old (-P) or new (-N) passphrases on the command line. Remember that any passwords specified on the command line will be saved in your shell history.
See the ssh-keygen man page for additional options.
Rotating keys
While the public key by itself is meant to be shared, keep in mind that if someone obtains your private key, they can then use that to access all systems that have the public key. These key pairs also do not have a period of validity like GNU Privacy Guard (GPG) keys or public key infrastructure (PKI) certificates.
If you have any reason to suspect that a private key has been stolen or otherwise compromised, you should replace that key pair. The old public key has to be removed from all systems, a new key has to be generated with ssh-keygen, and the new public key has to be transferred to the desired remote systems.
If you are rotating keys as a precaution and without any concern of compromise, you can use the old key pair to authenticate the transfer of the new public key before removing the old key.
Is using empty passphrases ever a good idea?
There are several things to think about when considering an empty passphrase for your SSH private key.
How secure is the private key file?
If you tend to work from multiple client systems and want to either have multiple copies of your key or keep a copy on removable media, then it really is a good idea to have a passphrase on the private key. This practice is in addition to protecting access to the key file with encrypted media.
However, if you have only one copy of the private key and it is kept on a system that is well secured and not shared, then having a passphrase is simply one more level of protection just in case.
Remember that changing the passphrase on one copy does not change the passphrase on other copies. The passphrase is simply locking access to a specific key file.
Why do think you need an empty passphrase?
There are cases for keys with empty passphrases. Some utilities that need to automatically transfer files between systems need a passwordless method to authenticate. The kdump utility, when configured to dump the kernel to a remote system using SSH, is one example.
Another common use is to generate a key pair for a script that is designed to run unattended, such as from a cron job.
How about a middle ground alternative?
By itself, a passphrase-protected private key requires the passphrase to be entered each time the key is used. This setup does not feel like passwordless SSH. However, there are caching mechanisms that allow you to enter the key passphrase once and then use the key over and over without reentering that passphrase.
More Linux resources
OpenSSH comes with an ssh-agent daemon and an ssh-add utility to cache the unlocked private key. The GNOME desktop also has a keyring daemon that stores passwords and secrets but also implements an SSH agent.
The lifetime of the cached key can be configured with each of the agents or when the key is added. In many cases, it defaults to an unlimited lifetime, but the cache is cleared when the user logs out of the system. You will be prompted for the passphrase only once per login session.
If there is a scheduled application that needs to run outside of a user login session, it may be possible to use a secret or other password manager to automate the unlocking of the key. For example, Ansible Tower stores credentials in a secure database. This database includes an SSH private key used to connect to the remote systems (managed nodes), and any passphrases necessary for those private keys. Once those credentials are stored, a job can be scheduled to run a playbook on a regular schedule.
Automating propagation
A centralized identity manager such as FreeIPA can assist with key propagation. Upload the public key to the server as an attribute of a user account, and then propagate it to the hosts in the domain as needed. FreeIPA can also provide additional host-based access control for where a key may be used.
Keys can also be distributed using Ansible modules. The openssh_keypair module uses ssh-keygen to generate keys and the authorized_key module adds and removes SSH authorized keys for particular user accounts.
Wrapping up
SSH key pairs are only one way to automate authentication without passwords. Using the Generic Security Services Application Program Interface (GSSAPI) authentication is also common when trying to reduce the use of passwords on a network with centralized user management. SSH key pairs are the easier option to implement when single sign-on (SSO) is not already available.
Many source code repositories grant access using SSH keys. You can upload a public key to an account in the hosting organization such as the Fedora Account System, GitLab, or GitHub sites and use that key pair to authenticate when pulling and pushing content to repositories.
Free Event: Red Hat Summit 2020 Virtual Experience
Attend the Red Hat Summit 2020 virtual experience, April 28-29.