Jun 29, 2017 I'm trying to connect in SSH to my AWS EC2 into my bitbucket pipelines. I've generate and setup a KEY pair in AWS (Key pair name: ShareaDreamKP) From this, I add the public key and private key into my bitbucket SSH keys I also add all my know host. Then, when I try to connect in SSH using this. Apr 12, 2018 SSH-key-based authentication provides a more secure alternative to password-based authentication. In this tutorial we'll learn how to set up SSH key-based authentication on an Ubuntu 16.04 installation.
Introduction
Establishing an SSH (Secure Shell) connection is essential to log in and effectively manage a remote server. Encrypted keys are a set of access credentials used to establish a secure connection.
This guide will walk you how to generate SSH keys on Ubuntu 18.04. We will also cover setting up SSH key-based authentication to connect to a remote server without requiring a password.
- A server running Ubuntu 18.04
- A user account with sudo privileges
- Access to a terminal window / command line (Ctrl-Alt-T)
If you are already running an Ubuntu 18.04 server, you can skip this step. If you are configuring your server for the first time, you may not have SSH installed.
1. Start by installing the tasksel package:
The system will first ask for confirmation before proceeding:
2. Next, use tasksel to install the ssh-server:
3. Load the SSH server service, and set it to launch at boot:
On your client system – the one you’re using to connect to the server – you need to create a pair of key codes.
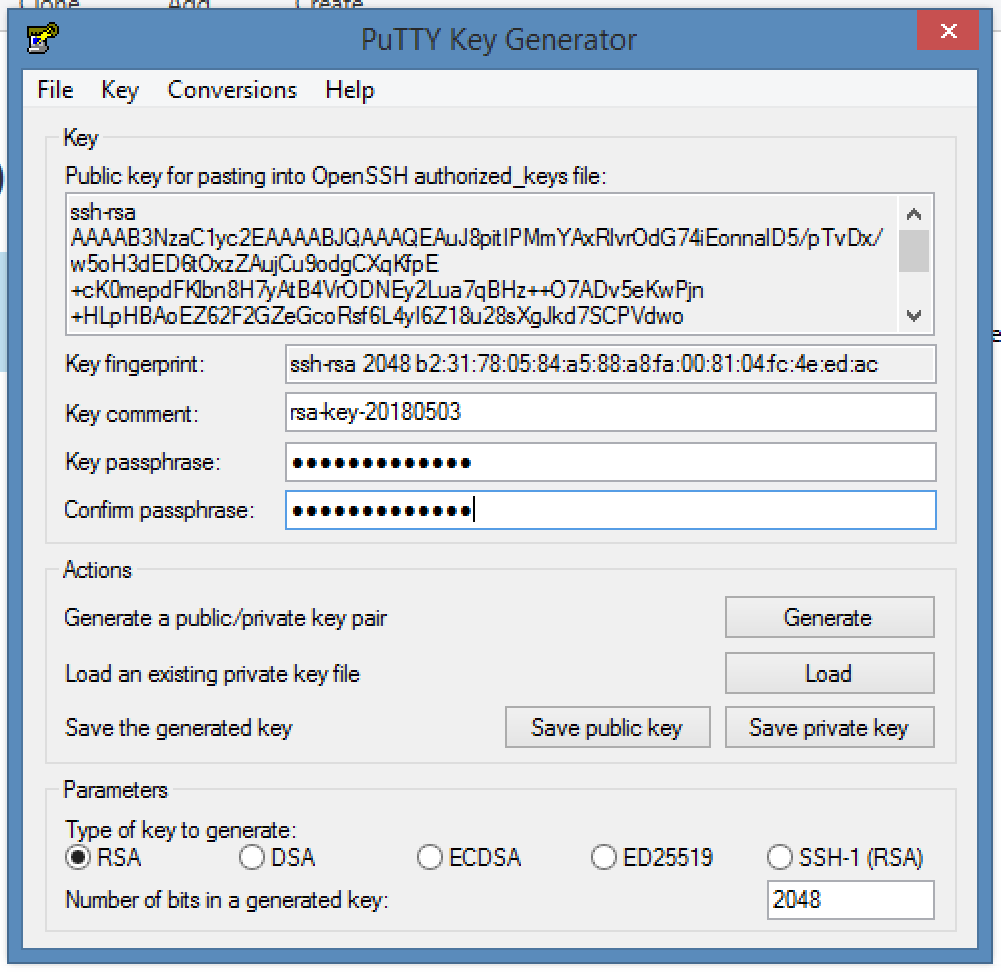
To generate a pair of SSH key codes, enter the commands:
This will create a hidden directory to store your SSH keys, and modify the permissions for that directory. The ssh-keygen command creates a 2048-bit RSA key pair.
For extra security, use RSA4096:
If you’ve already generated a key pair, this will prompt to overwrite them, and those old keys will not work anymore.
The system will ask you to create a passphrase as an added layer of security. Input a memorable passphrase, and press Enter.
This process creates two keys. One is a public key, which you can hand out to anyone – in this case, you’ll save it to the server. The other one is a private key, which you will need to keep secure. The secure private key ensures that you are the only person who can encrypt the data that is decrypted by the public key.
Step 2- Copy Public Key to the Ubuntu Server
First, get the IP address of the Ubuntu server you want to connect to.
In a terminal window, enter:
The system’s IP address is listed in the second entry:
On the client system, use the ssh-copy-id command to copy the identity information to the Ubuntu server:
Replace server_IP with the actual IP address of your server.
If this is the first time you’re connecting to the server, you may see a message that the authenticity of the host cannot be established:
Type yes and press Enter.
The system will check your client system for the id_rsa.pub key that was previously generated. Then it will prompt you to enter the password for the server user account. Type it in (the system won’t display the password), and press Enter.
The system will copy the contents of the ~/.ssh/id_rsa.pub from the client system into the ~/.ssh/authorized_keys directory of the server system.
The system should display:
If your system does not have the ssh-copy-id command, you can copy the key manually over the SSH.
Use the following command:
To log in to a remote server, input the command:
The system should not ask for a password as it is negotiating a secure connection using the SSH keys. If you used a security passphrase, you would be prompted to enter it. After you do so, you are logged in.
If this is the first time you’ve logged into the server, you may see a message similar to the one in part two. It will ask if you are sure you want to connect – type yes and press Enter.
Step 4- Disable Password Authentication
This step creates an added layer of security. If you’re the only person logging into the server, you can disable the password. The server will only accept a login with your private key to match the stored public key.
Edit the sshd_config file:
Search the file and find the PasswordAuthentication option.
Edit the file and change the value to no:
Save the file and exit, then restart the SSH service:
Verify that SSH is still working, before ending the session:
If everything works, you can close out and resume work normally.
By following the instructions in this tutorial, you have setup SSH-key-based authentication on an Ubuntu 18.04 server.
The connection is now highly secure as it uses a set of unique, encrypted SSH keys.
Next you should also read

Learn how to set up SSH key authentication on CentOS to safely communicate with remote servers. Create the…
When establishing a remote connection between a client and a server, a primary concern is ensuring a secure…
Nginx is an open-source server utility designed to work as a reverse proxy, intercepting client requests and…
Warcraft 3 the frozen throne free cd key generator. In this tutorial, Find out How To Use SSH to Connect to a Remote Server in Linux or Windows. Get started with…
- Azure
- Monitoring Azure services
- Azure Cross-Platform Command-Line Interface (xplat-cli)
- Linux
How to install Ansible to Ubuntu 14.04 LTS:
Monitoring Azure services
Monitoring Linux VM
Azure VM Extension IaaSDiagnostics (Azure Diagnostics Extension) is not yet supported in Linux VMs.
Azure management portal supports alert rules that send email alerts on following KPIs:
- Network In (Bytes)
- Network Out (Bytes)
- CPU Percentage (%)
- Disk Write Bytes/sec (Bytes/s)
- Disk Read Bytes/sec (Bytes/s)
Select the cloud service the virtual machine belongs to: monitor-tab > add metrics and then add rule.
Azure Cross-Platform Command-Line Interface (xplat-cli)
Instructions how to install and run xplat-cli in Ubuntu 14.04 LTS with bash.
Installation
- Sources in GitHub
xplat-cli runs on node.js platform so install node.js first.
Install bash completion too:
Install xplat-cli and configure bash completion:
Update
Later you'll need to update xplat-cli:
Update the bash completion too.
Login with account based authentication
Account based authentication relies on tokens that will expire at some point so re-authentication will be required. Two different types of accounts can be used:
- Azure organizational accounts
Login with Microsoft account requires one to open a web page where one have to enter an authentication code provided by the azure login command.
Note that you can log in to multiple accounts at the same time.
Login with a certificate
Earlier known also as a publishsettings file.
The certificate never expires.
Set Mode
Use Azure Resource Manager (ARM). Resource Manager overview. The ARM is not the default mode.
Create Azure Linux VM
Useful resources:
List available VM images:
List available VM locations:
List your virtual machines:
Generate certificate:
myPrivateKey.keyis the private key that have to be kept secretmyCert.pemis the public key
Create a virtual machine:
Add SSH endpoint ACL:
Export VM role file the can be used later with vm create-from to re-create the VM. See also Exporting and Importing VM settings with the Azure Command-Line Tools.
Create Azure Blob Storage
Useful tools:
The storage URL is in format:
Note that there is really only one container level-hierarchy. If the URL seems to have more containers they are in fact part of the blob name.
Create new storage account and set the access key:
Create new container:
List blobs in container:
Configuration file: ~/.ssh/config
Generate ssh-keys:
See also: https://help.github.com/articles/generating-ssh-keys/
SSH agent:
SSH local port forwarding:
SSH key based authentication:
sshd essential configuration (/etc/ssh/sshd_config):
Restart sshd in CentOS7: systemctl restart sshd.service
Get server certificates:
Save server certificate (1st in the chain) to a file (PEM/DER). Note the other certificates in the chain are ignored:
Show certificate information:
Certificate fingerprints:
Check server SSL configuration with openssl:
Use -R option for recursion.
Generate Ssh Key Ubuntu Bitbucket Version
CentOS
Ubuntu
Replace A String In File
Generate Ssh Key Ubuntu Bitbucket Server
Random String
TODO
- My Vagrant Base Boxes
- Keep VirtualBox guest additions up-to-date with https://github.com/dotless-de/vagrant-vbguest
Troubleshooting ssh configuration:
Updated