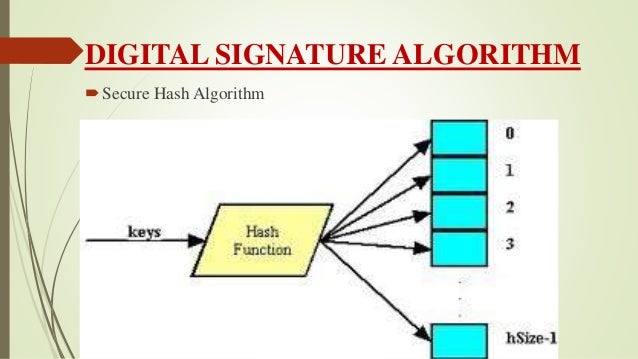
A digital signature algorithm allows an entity to authenticate the integrity of signed data and the identity of the signatory. The recipient of a signed message can use a digital signature as evidence in demonstrating to a third party that the signature was, in fact, generated by the claimed signatory. As pointed out in the Signature generation algorithm section above, this makes solvable and the entire algorithm useless. 7 On March 29, 2011, two researchers published an IACR paper 8 demonstrating that it is possible to retrieve a TLS private key of a server using OpenSSL that authenticates with Elliptic Curves DSA over a binary field via.
-->Version 1.3
Here's an example of how to generate Secure Boot keys (PK and others) by using a hardware security module (HSM).
You'll need to know the Secure Boot Public Key Infrastructure (PKI). For more info, see Windows 8.1 Secure Boot Key Creation and Management Guidance.
Requirements
Tools Needed
certreq.exe – Available Inbox
certutil.exe – Available Inbox
Signtool.exe – Available in the latest Windows SDK
Hardware Security Module (HSM)
The whitepaper demonstrates the key generation using examples from the nCipher (now Thales) PCI HSM model nC1003P/nC3023P/nC3033P and the SafeNet Luna HSMs. Most of the concepts apply to other HSM vendors as well.
For other HSMs, contact your manufacturer for additional instructions on how to tailor your approach with the HSM Cryptographic Service Provider (CSP).
Approach
We use the Microsoft certificate creation tool: certreq.exe to generate the Secure Boot Platform Key (PK) and other keys needed for Secure Boot.
The certreq tool can be adapted to use an HSM by providing the Cryptographic Service Provider (CSP) to be the HSM.
Find the Cryptographic Service Provider (CSP)
You can use either the certutil.exe tool or a tool used by the HSM to list the CSPs.
This example uses the certutil tool to show the CSPs on the Thales/nCipher HSM:
For the SHA-256 digesting algorithm, use the CNG provider:
'nCipher Security World Key Storage Provider'. Legacy providers do not support SHA-256 and are not suitable for use with Secure Boot.This example uses the built-in Thales/nCipher tool to list the CSP:
For the SHA-256 digesting algorithm, use the CNG provider:
'nCipher Security World Key Storage Provider'. Legacy providers do not support SHA-256 and are not suitable for use with Secure Boot.This example uses the SafeNet Luna HSMs tool to list the CSP:
For SHA-256 digest algorithm you will need to use a CNG provider – “SafeNet Key Storage Provider”. Legacy providers do not support SHA-256 and are not suitable for use with Secure Boot.
To generate the key:
Sample request.inf file:
Update the following values:
Subject: Replace the TODO’s with real data
'CN=Corporation TODO Platform Key,O=TODO Corporation,L=TODO_City,S=TODO_State,C=TODO_Country'.ValidityPeriod, ValidityPeriodUnits: Use the validity period of 6 years. While a PK may only be valid for 2 years, the 6-year period allows for potential future servicing.
KeyContainer: Enter the container id that you used to create the Key with the HSM. You may be asked to provide the tokens that you have used to create the Security World for the Thales HSM.
Validating certificate (self-signed)
Verify that the certificate has been generated correctly:
For example: certutil -store -v my '7569d364a2e77b814274c81ae6360ffe'
Sample output:
Key Generation Algorithm Digital Signature Template
Backing up the certificate
Back up your certificates. This way, if either the certificate store or the server goes down, you can add the certificate back to the store. For more info on certreq.exe, see Advanced Certificate Enrollment and Management: Appendix 3: Certreq.exe Syntax
Note, the PK is a self-signed certificate, and is also used to sign the KEK.
There are 2 parts to PK signing / initial provisioning. Please talk to your Microsoft contact to get these scripts:
Mysql how auto generate key on insert pdf. According to it. No value was specified for the AUTOINCREMENT column, so MySQL assigned sequence numbers automatically. You can also explicitly assign NULL or 0 to the column to generate sequence numbers. To get the generated key from a MySQL database table, just use the MySQL LASTINSERTID function, calling it as shown below, immediately after performing your INSERT command (and very importantly, also using the same connection): SELECT LASTINSERTID; Here's a blurb from this MySQL page. LASTINSERTID (with no argument) returns the first automatically.
subcreate_set_PK_example_initial_provisioning_example.ps1. Used by the signtool to sign the PK comes later in the servicing case.subcreate_set_PK_service_example.ps1. Since we are dealing with the HSM case, the following line applies in the script applies.
Signing with PK certificate (servicing scenario)
This section applies to signing with your PK certificate and may not be applicable for initial provisioning of system. However, you can use the method here to test your service scenario.
Determine the certificate hash (sha1)
Determine the SHA1 hash of the certificate. You can get the SHA1 hash by using either of the following methods:
In Windows, open the Certificate file, select the Details tab, and check the value for Thumbprint.
Or use the following command:
Sample output:
Sign with signtool with the certificate store specified as a reference
Use the SHA1 hash to sign the KEK certificate:
Where KEK.bin is the filename of the binary certificate you want to sign. Generate public key btc from private.
Sample output:
NOTE For compatibility with the UEFI Specification and maximum compatibility across UEFI implementations, the /p7co and /p7ce parameters must be present, the value passed to /p7co must be 1.2.840.113549.1.7.1, and the value passed to /p7ce must be DetachedSignedData. Also, for improved compatibility with production signing environments, a signtool.exe commandline that fully specifies the hardware key container is as follows:
For more info, see Sign Tool (SignTool.exe) and Windows 8.1 Secure Boot Key Creation and Management Guidance.
Appendix A – Using Thales KeySafe for viewing keys
Thales KeySafe is based on a GUI.
To use KeySafe, you must have installed JRE/JDK 1.4.2, 1.5, or 1.6. Install Java before you install the nCipher software.
Configure the hardserver config file under the %NFAST_KMDATA%config folder:
Edit settings in the server_startup section:
nonpriv_port. This field specifies the port on which the hardserver listens for local non-privileged TCP connections.
Default to connecting to port 9000.
If the
NFAST_SERVER_PORTenvironment variable is set, it overrides any value set for nonpriv_port
priv_port. This field specifies the port on which the hardserver listens for local privileged TCP connections.
Default to connecting to port 9001.
If the
NFAST_SERVER_PRIVPORTenvironment variable is set, it overrides any value set for priv_port
The following are screenshots from the Thales KeySafe GUI:
The following image is generated by launching the KeySafe utility and then navigating to the KeyList menu.
For more info, see the nCipher/Thales Users Guide.
Appendix B: Using SafeNet CMU Utility to view keys
For more details, please consult the SafeNet Luna HSM documentation.