Key authentication is used to solve the problem of authenticating the keys of the person (say 'person B') to whom some other person ('person A') is talking to or trying to talk to. In other words, it is the process of assuring that the key of 'person A' held by 'person B' does in fact belong to 'person A' and vice versa.
- Key Generation In Asymmetric Authentication Definition
- Key Generation In Asymmetric Authentication Form
Key Generation In Asymmetric Authentication Definition
Symmetric encryption algorithms use pre-shared keys. Asymmetric encryption algorithms use different keys to encrypt and decrypt data. Authentication, and confidentiality are the three objectives of secure communications. Pre-shared key generation symmetric encryption algorithms.
This is usually done after the keys have been shared among the two sides over some secure channel, although some of the algorithms share the keys at the time of authentication also.
The simplest solution for this problem is for the two users concerned to meet face-to-face and exchange keys. However, for systems in which there are a large number of users or in which the users do not personally know each other (e.g., Internet shopping) this is not practical. There are various algorithms for both symmetric keys and asymmetric public key cryptography to solve this problem.
Authentication using Shared Keys[edit]
For key authentication using the traditional symmetric key cryptography, this is the problem of assuring that there is no man-in-the-middle attacker who is trying to read or spoof the communication. There are various algorithms used now-a-days to prevent such attacks. The most common among the algorithms are Diffie–Hellman key exchange, authentication using Key distribution center, kerberos and Needham–Schroeder protocol. Other methods that can be used include Password-authenticated key agreement protocols etc.[1]
Authentication using Public Key Cryptography[edit]
Crypto systems using asymmetric key algorithms do not evade the problem either. That a public key can be known by all without compromising the security of an encryption algorithm (for some such algorithms, though not for all) is certainly useful, but does not prevent some kinds of attacks. For example, a spoofing attack in which public key A is claimed publicly to be that of user Alice, but is in fact a public key belonging to man-in-the-middle attackerMallet, is easily possible. No public key is inherently bound to any particular user, and any user relying on a defective binding (including Alice herself when she sends herself protected messages) will have trouble.
The most common solution to this problem is the use of public key certificates and certificate authorities (CAs) for them in a public-key infrastructure (PKI) system. The certificate authority (CA) acts as a 'trusted third party' for the communicating users and, using cryptographic binding methods (e.g., digital signatures) represents to both parties involved that the public keys each holds which allegedly belong to the other, actually do so. A digital notary service, if you will. Such CAs can be private organizations providing such assurances, or government agencies, or some combination of the two. However, in a significant sense, this merely moves the key authentication problem back one level for any CA may make a good faith certification of some key but, through error or malice, be mistaken. Any reliance on a defective key certificate 'authenticating' a public key will cause problems. As a result, many people find all PKI designs unacceptably insecure.

Accordingly, key authentication methods are being actively researched.
See also[edit]
- Public-key infrastructure (PKI)
- Identity based encryption (IBE)
References[edit]
- ^Tanenbaum, Andrew S.; Wetherall, David J. (7 October 2010). 'Computer Networks'. Pearson – via Amazon.
External links[edit]
Cryptography
Derrick Rountree, in Security for Microsoft Windows System Administrators, 2011
Asymmetric Encryption
Asymmetric encryption is also referred to as public key encryption. In asymmetric encryption, both the encrypting and decrypting systems have a set of keys. One is called the public key, and another is called the private key. If the message is encrypted with one key in the pair, the message can be decrypted only with the other key in the pair.
Asymmetric key algorithms are not quite as fast as symmetric key algorithms. This is partially due to the fact that asymmetric key algorithms are generally more complex, using a more sophisticated set of functions.
Asymmetric Key Algorithms
Asymmetric key algorithms aren't as widely used as their symmetric counterparts. So we'll just go over two of the big ones: Diffie-Hellman and RSA.
Key Generation In Asymmetric Authentication Form
Diffie-Hellman: The Diffie-Hellman algorithm was one of the earliest known asymmetric key implementations. The Diffie-Hellman algorithm is mostly used for key exchange. Although symmetric key algorithms are fast and secure, key exchange is always a problem. You have to figure out a way to get the private key to all systems. The Diffie-Hellman algorithm helps with this. The Diffie-Hellman algorithm will be used to establish a secure communication channel. This channel is used by the systems to exchange a private key. This private key is then used to do symmetric encryption between the two systems.
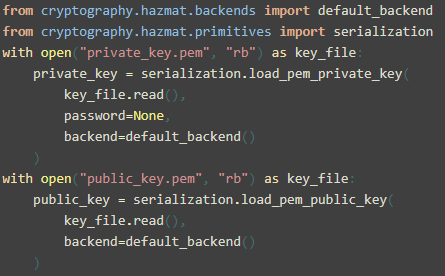
RSA: It is the Rivest Shamir Adelman algorithm. RSA was developed in 1978. RSA was the first widely used asymmetric algorithms used for signing and encryption. It supports key lengths of 768 and 1,024 bits. The RSA algorithm uses a three-part process. The first part is key generation. The keys used in the RSA algorithm are generated using mathematical operations based on prime numbers. The second part of the process is encryption. This encryption is done using one of the keys in the key pair. The third part of the process is decryption. The decryption is done using the other key in the key pair.
Update: I happen to read that checksum function is not guaranteed to give unique values. said,August 4, 2008@. Hash key generator sql server with set output. This is the case with SQL Server 2000 and I believe the same case with SQL Server 2005.
Read full chapter