Tomcat-users Tomcat and SSL; Kevin Pang. May 14, 2001 at 5:48 pm: Hi All. Key pair not generated, alias already exists I never use SSL before and very confused now, are there some documentation to do this step by step? Any help are highly appreciated!
Related Topics:
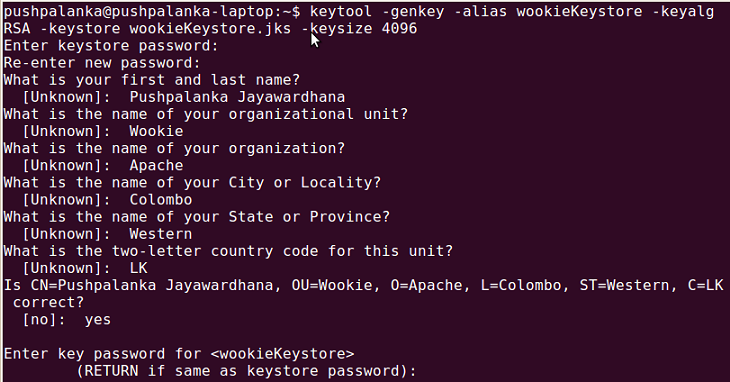
'keytool -genkeypair' Command Examples - Generate Key Pair
How to use the 'keytool -genkeypair' command? I want to generate a pair of public key and private key for myself. Here is an example of using 'keytool -genkeypair' command to generate a pair of public key and private key for yourself: C:Usersfyicenter>'Program Filesjavajre7binkeytool' -genkey.. 2012-07-19, 17349👍, 0💬
'keytool -exportcert' Command Examples - Exporting Certificate
How to use the 'keytool -exportcert' command? I want to export a certificate out of a keystore file and send it to someone else. Here is an example of using 'keytool -exportcert' command to export the self-signed certificate in the '2ndkey' entry from the default keystore file: C:Usersfyicenter>'.. 2012-07-19, 16396👍, 0💬
- Jul 09, 2019 All the information sent from a browser to a website server is encrypted with the Public Key, and gets decrypted on the server side with the Private Key. Together the key pair keeps communication secured, and one key will not work without the other. How do I get it? The Private Key is generated with your Certificate Signing Request (CSR).
- On the Key Pairs page in the Amazon EC2 console, the Fingerprint column displays the fingerprints generated from your key pairs. AWS calculates the fingerprint differently depending on whether the key pair was generated by AWS or a third-party tool.
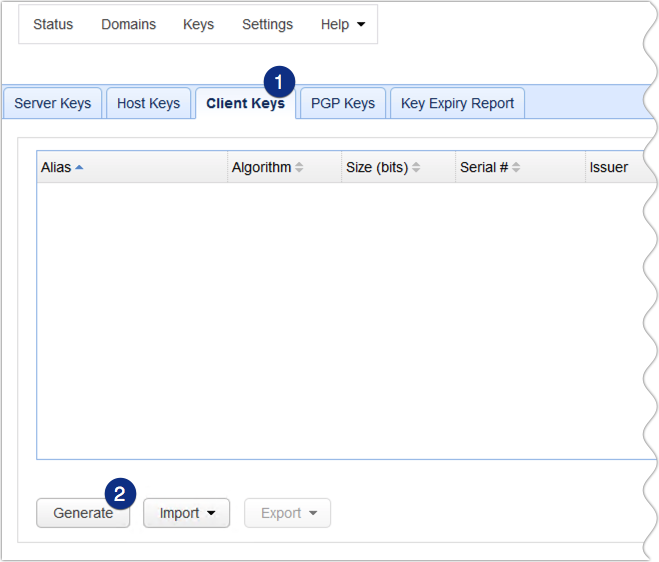
- If the selected file was not a PEM bundle containing key pairs, the PKCS #12 Keystore Password dialog will appear. Enter the PKCS #12 keystore's password into the dialog and press OK. The Import Key Pair dialog will appear populated with the aliases of all key pairs.
- You should not try to convert a keystore that contains secret keys to either JKS or PKCS#12. Export public key certificate from a keystore The following command exports the public key certificate created in section 'Generate a public/private key pair and a self-signed certificate' to a.
Java 'keytool -genkeypair' Command Options
What options are supported by the 'keytool -genkeypair' command? Java Keytool can be used to generate a pair of public key and private key with the 'keytool -genkeypair' command, which supports the following options: C:Usersfyicenter>'Program Filesjavajre7binkeytool' -genkeypair -help keytool.. 2012-07-19, 13381👍, 0💬
Help on Using the Java Keytool Command
How to get help on using the Java Keytool command? I have never used Keytool before. If you are new to the Java Keytool, you should first read the documentation: keytool - Key and Certificate Management Tool. Java Keytool is a command line tool. You need to run it from a command line window using th.. 2012-07-19, 11570👍, 0💬
Java 'keytool -exportcert' Command Options
What options are supported by the 'keytool -exportcert' command? Java Keytool can be used to export a single certificate out of a key store file with the 'keytool -exportcert' command which supports the following options: C:Usersfyicenter>'Program Filesjavajre7binkeytool' -exportcert -help ke.. 2012-07-19, 8676👍, 0💬
[ aws . kms ]
Description¶
Generates a unique asymmetric data key pair. The GenerateDataKeyPairWithoutPlaintext operation returns a plaintext public key and a copy of the private key that is encrypted under the symmetric CMK you specify. Unlike GenerateDataKeyPair , this operation does not return a plaintext private key.
To generate a data key pair, you must specify a symmetric customer master key (CMK) to encrypt the private key in the data key pair. You cannot use an asymmetric CMK. To get the type of your CMK, use the KeySpec field in the DescribeKey response.
You can use the public key that GenerateDataKeyPairWithoutPlaintext returns to encrypt data or verify a signature outside of AWS KMS. Then, store the encrypted private key with the data. When you are ready to decrypt data or sign a message, you can use the Decrypt operation to decrypt the encrypted private key.
You can use the optional encryption context to add additional security to the encryption operation. If you specify an EncryptionContext , you must specify the same encryption context (a case-sensitive exact match) when decrypting the encrypted data key. Otherwise, the request to decrypt fails with an InvalidCiphertextException. For more information, see Encryption Context in the AWS Key Management Service Developer Guide .
The CMK that you use for this operation must be in a compatible key state. For details, see How Key State Affects Use of a Customer Master Key in the AWS Key Management Service Developer Guide .
See also: AWS API Documentation
See 'aws help' for descriptions of global parameters.
Synopsis¶
Options¶
--encryption-context (map)
Specifies the encryption context that will be used when encrypting the private key in the data key pair.
An encryption context is a collection of non-secret key-value pairs that represents additional authenticated data. When you use an encryption context to encrypt data, you must specify the same (an exact case-sensitive match) encryption context to decrypt the data. An encryption context is optional when encrypting with a symmetric CMK, but it is highly recommended.
For more information, see Encryption Context in the AWS Key Management Service Developer Guide .
Shorthand Syntax:
JSON Syntax:
--key-id (string)
Specifies the CMK that encrypts the private key in the data key pair. You must specify a symmetric CMK. You cannot use an asymmetric CMK. To get the type of your CMK, use the DescribeKey operation.
To specify a CMK, use its key ID, Amazon Resource Name (ARN), alias name, or alias ARN. When using an alias name, prefix it with 'alias/' .
For example:
- Key ID: 1234abcd-12ab-34cd-56ef-1234567890ab
- Key ARN: arn:aws:kms:us-east-2:111122223333:key/1234abcd-12ab-34cd-56ef-1234567890ab
- Alias name: alias/ExampleAlias
- Alias ARN: arn:aws:kms:us-east-2:111122223333:alias/ExampleAlias
To get the key ID and key ARN for a CMK, use ListKeys or DescribeKey . To get the alias name and alias ARN, use ListAliases .
--key-pair-spec (string)
Determines the type of data key pair that is generated.
The AWS KMS rule that restricts the use of asymmetric RSA CMKs to encrypt and decrypt or to sign and verify (but not both), and the rule that permits you to use ECC CMKs only to sign and verify, are not effective outside of AWS KMS.
Key Pair Not Generated Alias Already Exists
Possible values:
- RSA_2048
- RSA_3072
- RSA_4096
- ECC_NIST_P256
- ECC_NIST_P384
- ECC_NIST_P521
- ECC_SECG_P256K1
--grant-tokens (list)
A list of grant tokens.
For more information, see Grant Tokens in the AWS Key Management Service Developer Guide .
Syntax:
--cli-input-json (string)Performs service operation based on the JSON string provided. The JSON string follows the format provided by --generate-cli-skeleton. If other arguments are provided on the command line, the CLI values will override the JSON-provided values. It is not possible to pass arbitrary binary values using a JSON-provided value as the string will be taken literally.
--generate-cli-skeleton (string)Prints a JSON skeleton to standard output without sending an API request. If provided with no value or the value input, prints a sample input JSON that can be used as an argument for --cli-input-json. If provided with the value output, it validates the command inputs and returns a sample output JSON for that command.
Terminal generate ssh key. See 'aws help' for descriptions of global parameters.
Output¶
PrivateKeyCiphertextBlob -> (blob)
PublicKey -> (blob)
KeyId -> (string)
Specifies the CMK that encrypted the private key in the data key pair. You must specify a symmetric CMK. You cannot use an asymmetric CMK. To get the type of your CMK, use the DescribeKey operation.
To specify a CMK, use its key ID, Amazon Resource Name (ARN), alias name, or alias ARN. When using an alias name, prefix it with 'alias/' .
For example:
- Key ID: 1234abcd-12ab-34cd-56ef-1234567890ab
- Key ARN: arn:aws:kms:us-east-2:111122223333:key/1234abcd-12ab-34cd-56ef-1234567890ab
- Alias name: alias/ExampleAlias
- Alias ARN: arn:aws:kms:us-east-2:111122223333:alias/ExampleAlias
To get the key ID and key ARN for a CMK, use ListKeys or DescribeKey . To get the alias name and alias ARN, use ListAliases .
Key Pair Not Generated Alias Already Exists
KeyPairSpec -> (string)