- Puttygen Key Generator
- Puttygen Generate Key From Pub File Online
- Puttygen Generate Key From Pub File Download
- Puttygen Generate Key From Pub File Free
PuTTY does not natively support the private key format for SSH keys. PuTTY provides a tool named PuTTYgen, which converts keys to the required format for PuTTY. You must convert your private key (.pem file) into this format (.ppk file) as follows in order to connect to your instance using PuTTY. The Solution: When you get to the public key screen in creating your key pair in puttygen, copy the public key and paste it into a text file with the extension.pub. You will save you sysadmin hours of frustration reading posts like this. The.pub file is your public key, and the other file is the corresponding private key. If you don’t have these files (or you don’t even have a.ssh directory), you can create them by running a program called ssh-keygen, which is provided with the SSH package on Linux/macOS systems and comes with Git for Windows. NOTE: You can also use puttygen to import ssh style PEM files back into putty. PuTTY's author opted for simplicity so the public and private keys which make up the underlying security used by putty/ssh 2 key authentication are stored in a single proprietary.ppk file. Typically these keys are maintained as a 2 separate files by ssh. On Linux the key files are typically kept in the directory,.ssh. There is a good overview of the conversion process here in this Stack Overflow question titled.
PuTTYgen, part of the open source network networking client PuTTY, is a crucial generating tool to create public and private SSH keys for servers. The native file format of PuTTY is .ppk files. Additionally, the tool is used for SSH connectivity. So users can use PuTTY to connect and securely transfer data from localhost to remote system.
But to use PuTTY, the private keys must be in the native format of the application. So for example, as Amazon Elastic Compute Cloud (EC2), a core part of the cloud-computing platform, generates Privacy-Enhanced Mail (PEM) file format, a user must first convert the file to .ppk file format before connecting to Linux Instance (virtual server on Amazon Web Services) from a Windows machine.
The EC2 allows users to lease virtual systems so that they can run their applications on it.
Puttygen Key Generator
However if one plans to use PuTTY’s SSH client to connect, then they are first required to convert the .pem file to .ppk using PuTTYgen and then use PuTTY application to join local and remote hosts.
- 4 Converting .Pem to .Ppk on Unix or Linux
What Is the .Pem File Format?
Privacy-Enhanced Mail (PEM) file extension is a format that is mainly used to transmit data, certificates, email and cryptographic keys privately. The PEM file format is a tamperproof and secure way of storing and transferring data.
As a ‘.pem file’ can store multiple types of data; it represents data with appropriate suffix. While the most common is .pem suffix, others include .key for private keys and .cer or .crt for certificates. The PEM file format encodes it with the binary-to-text encoding scheme – base64 so that it represents binary data in ASCII string.
Even though the technological advancements have led to a more secure alternative to PEM container, it is still leveraged to store public and private certificates, root certificates and many others.
Unlike most file formats that are easy to convert via online conversion tools, a user requires a specific application to convert files that have .pem extensions. PuTTYgen is one such application that quickly converts f .pem files to .ppk.
Convert .Pem to .Ppk using PuTTYgen
The primary requisite is to download and install PuTTY application. As part of the networking client, PuTTYgen does not have to be downloaded separately. Users must download the latest version of the app and install the entire suite. Once installed, PuTTYgen will be ready to convert .pem files to .ppk format. We will provide detail steps to convert files on both operating systems – Windows and Unix.
Converting .Pem to .Ppk on Windows
- Click on Start menu> All Programs > PuTTY > PuTTYgen.
- The following window will present with options on the crucial a user wants to generate. Select the option ‘RSA (Rivest–Shamir–Adleman). RSA is a public-key cryptosystem that is commonly used to transmit data securely. Users with an older version of PuTTY should select the option – ‘SSH-2 RSA.’
- Next, click on the option ‘Load.’ As PuTTY supports its native file format, it will only show files that have .ppk file extension. Therefore, users have to choose the ‘All Files’ option from the drop-down bar. It will display all key files included the .pem file.
- Now, select the .pem file that you want to convert. As aforementioned that PuTTYgen is used for SSH connectivity, so it crucial for users to select the specific file that they plan to convert and click ‘Open.’ To confirm, click on ‘OK.’
- In the resultant window, click on ‘Save private key’ which will convert and save the key file in PuTTY compatible format.
- PuTTYgen will prompt a warning of saving the key without a passphrase. Hit ‘Yes’ on it.
- Now, give the name to your file and PuTTYgen will automatically add .ppk file extension.
Note – Passphrases provide extra protection, but it sometimes gets annoying as each time a user copies files they have to enter the passphrase. Although, it entirely depends on the user if they wish or don’t wish to add the extra layer of protection
Once the file is converted to PuTTY compatible format, users can connect their local machine with remote servers.
Converting .Pem to .Ppk on Unix or Linux
To convert the file on Unix is far simpler than Windows. Users are first required to install PuTTY application on their Unix machines. Once done, all a user must do is enter a one-line command. First, run the PuTTYgen command and type the below-written command:
$ sudo puttygen pemKey.pem -o ppkKey.ppk -O private
Voila! The .pem files will quickly be converted to PuTTY native file format. Users can connect via PuTTY to remote servers from local systems using the newly created .ppk files on both Windows and Unix.
Connect Using PuTTY
Puttygen Generate Key From Pub File Online
Once the .pem file is converted .ppk then users can connect to remote hosts using PuTTY’s SSH client. Below are steps to launch a PuTTY session.
- First, open PuTTY and input the host IP address. Please note that an SSL VPN connection must be established if the connection is to with 10.X private address.
- Now, from the category pane, navigate to Connection and expand SSH and the Auth.
- Click on ‘Browse’ and select the newly converted .ppk file, that was generated using PuTTYgen.
- Now to commence the PuTTY session, choose the option ‘open.’
Note: If the remote and local hosts connect for the first time using PuTTY then the application will pop up a dialog box confirming the authenticity of the connection. It just provides an added layer of security, so click ‘Yes’ when it appears.
Transferring Files Using PuTTY
Interestingly, one can also use PuTTY applications another component the PuTTY Secure Copy client (PSCP) to transfer files to remote servers. The PSCP is a Secure copy protocol (SCP) client that enables secure transfer of files from localhost to remote hosts.
Puttygen Generate Key From Pub File Download
If users are not comfortable using the command-line tool they can choose another Graphic user interface-based SCP client. One of the notable is WinSCP – an open-source multi-protocol supportive application for Microsoft Windows.
Back to PSCP, users are required to use the private key they generated while converting the .pem file to the .ppk file.
Puttygen Generate Key From Pub File Free
Converting a .pem file to a .ppk using PuTTYgen may now seem simple. The above information also briefs users on using PuTTY’s SSH client to connect virtual servers with local machines.
Before you begin
Using SSH public-key authentication to connect to a remote system is a robust, more secure alternative to logging in with an account password or passphrase. SSH public-key authentication relies on asymmetric cryptographic algorithms that generate a pair of separate keys (a key pair), one 'private' and the other 'public'. You keep the private key a secret and store it on the computer you use to connect to the remote system. Conceivably, you can share the public key with anyone without compromising the private key; you store it on the remote system in a .ssh/authorized_keys directory.
To use SSH public-key authentication:
- The remote system must have a version of SSH installed. The information in this document assumes the remote system uses OpenSSH. If the remote system is using a different version of SSH (for example, Tectia SSH), the process outlined below may not be correct.
- The computer you use to connect to the remote server must have a version of SSH installed. This document includes instructions for generating a key pair with command-line SSH on a Linux or macOS computer, and with PuTTY on a Windows computer.
- You need to be able to transfer your public key to the remote system. Therefore, you must either be able to log into the remote system with an established account username and password/passphrase, or have an administrator on the remote system add the public key to the
~/.ssh/authorized_keysfile in your account. - Two-factor authentication using Two-Step Login (Duo) is required for access to the login nodes on IU research supercomputers, and for SCP and SFTP file transfers to those systems. SSH public-key authentication remains an option for researchers who submit the 'SSH public-key authentication to HPS systems' user agreement (log into HPC everywhere using your IU username and passphrase), in which you agree to set a passphrase on your private key when you generate your key pair. If you have questions about how two-factor authentication may impact your workflows, contact the UITS Research Applications and Deep Learning team. For help, see Get started with Two-Step Login (Duo) at IU and Help for Two-Step Login (Duo).
Set up public-key authentication using SSH on a Linux or macOS computer
To set up public-key authentication using SSH on a Linux or macOS computer:
- Log into the computer you'll use to access the remote host, and then use command-line SSH to generate a key pair using the RSA algorithm.
To generate RSA keys, on the command line, enter:
- You will be prompted to supply a filename (for saving the key pair) and a password (for protecting your private key):
- Filename: To accept the default filename (and location) for your key pair, press
EnterorReturnwithout entering a filename.Alternatively, you can enter a filename (for example,
my_ssh_key) at the prompt, and then pressEnterorReturn. However, many remote hosts are configured to accept private keys with the default filename and path (~/.ssh/id_rsafor RSA keys) by default. Consequently, to authenticate with a private key that has a different filename, or one that is not stored in the default location, you must explicitly invoke it either on the SSH command line or in an SSH client configuration file (~/.ssh/config); see below for instructions. - Password: Enter a password that contains at least five characters, and then press
EnterorReturn. If you pressEnterorReturnwithout entering a password, your private key will be generated without password-protection.If you don't password-protect your private key, anyone with access to your computer conceivably can SSH (without being prompted for a password) to your account on any remote system that has the corresponding public key.
Your private key will be generated using the default filename (for example,
id_rsa) or the filename you specified (for example,my_ssh_key), and stored on your computer in a.sshdirectory off your home directory (for example,~/.ssh/id_rsaor~/.ssh/my_ssh_key).The corresponding public key will be generated using the same filename (but with a
.pubextension added) and stored in the same location (for example,~/.ssh/id_rsa.pubor~/.ssh/my_ssh_key.pub). - Filename: To accept the default filename (and location) for your key pair, press
- Use SFTP or SCP to copy the public key file (for example,
~/.ssh/id_rsa.pub) to your account on the remote system (for example,[email protected]); for example, using command-line SCP:You'll be prompted for your account password. Your public key will be copied to your home directory (and saved with the same filename) on the remote system.
- Log into the remote system using your account username and password.If the remote system is not configured to support password-based authentication, you will need to ask system administrators to add your public key to the
~/.ssh/authorized_keysfile in your account (if your account doesn't have~/.ssh/authorized_keysfile, system administrators can create one for you). Once your public key is added to your~/.ssh/authorized_keysfile on the remote system, the setup process is complete, and you should now be able to SSH to your account from the computer that has your private key. - If your account on the remote system doesn't already contain a
~/.ssh/authorized_keysfile, create one; on the command line, enter the following commands:If your account on the remote system already has a~/.ssh/authorized_keysfile, executing these commands will not damage the existing directory or file. - On the remote system, add the contents of your public key file (for example,
~/id_rsa.pub) to a new line in your~/.ssh/authorized_keysfile; on the command line, enter:You may want to check the contents of
~/.ssh/authorized_keysto make sure your public key was added properly; on the command line, enter: - You may now safely delete the public key file (for example,
~/id_rsa.pub) from your account on the remote system; on the command line, enter:Alternatively, if you prefer to keep a copy of your public key on the remote system, move it to your
.sshdirectory; on the command line, enter: - Optionally, repeat steps 3-7 to add your public key to other remote systems that you want to access from the computer that has your private key using SSH public-key authentication.
- You now should be able to SSH to your account on the remote system (for example,
[email protected]) from the computer (for example,host1) that has your private key (for example,~/.ssh/id_rsa):- If your private key is password-protected, the remote system will prompt you for the password or passphrase (your private key password/passphrase is not transmitted to the remote system):
- If your private key is not password-protected, the remote system will place you on the command line in your home directory without prompting you for a password or passphrase:
If the private key you're using does not have the default name, or is not stored in the default path (not
~/.ssh/id_rsa), you must explicitly invoke it in one of two ways:Developed by much of the same team that made Black Flag, Origins does away with tired AC elements like sync towers and minimap bloat to refocus on giant vistas to explore and satisfying action RPG combat to master. Cd-key generator left 4 dead. You can even ride a horse (or camel) into battle, trading in the stealth approach for a stylish entrance.
- On the SSH command line: Add the
-iflag and the path to your private key.For example, to invoke the private key
host2_key, stored in the~/.ssh/old_keysdirectory, when connecting to your account on a remote host (for example,[email protected]), enter: - In an SSH client configuration file: SSH gets configuration data from the following sources (in this order):
- From command-line options
- From the user's client configuration file (
~/.ssh/config), if it exists - From the system-wide client configuration file (
/etc/ssh/ssh_config)
The SSH client configuration file is a text file containing keywords and arguments. To specify which private key should be used for connections to a particular remote host, use a text editor to create a
~/.ssh/configthat includes theHostandIdentityFilekeywords.For example, for connections to
host2.somewhere.edu, to make SSH automatically invoke the private keyhost2_key, stored in the~/.ssh/old_keysdirectory, create a~/.ssh/configfile with these lines included:Once you save the file, SSH will use the specified private key for future connections to that host.
You can add multiple
HostandIdentityFiledirectives to specify a different private key for each host listed; for example:Alternatively, you can use a single asterisk (
*) to provide global defaults for all hosts (specify one private key for several hosts); for example:For more about the SSH client configuration file, see the OpenSSH SSH client configuration file on the web or from the command line (
man ssh_config).
Set up public-key authentication using PuTTY on a Windows 10 or Windows 8.x computer
The PuTTY command-line SSH client, the PuTTYgen key generation utility, the Pageant SSH authentication agent, and the PuTTY SCP and SFTP utilities are packaged together in a Windows installer available under The MIT License for free download from the PuTTY development team.
After installing PuTTY:
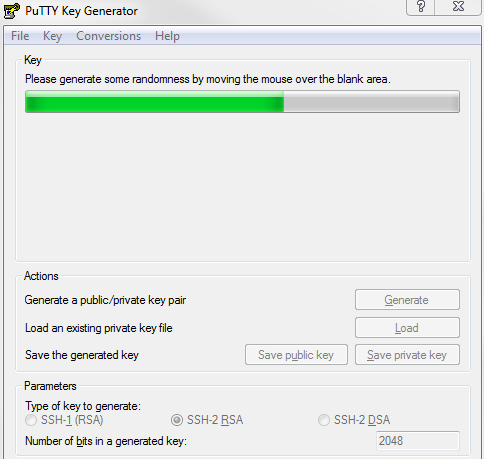
- Launch PuTTYgen.
- In the 'PuTTY Key Generator' window, under 'Parameters':
- For 'Type of key to generate', select RSA. (In older versions of PuTTYgen, select SSH2-RSA.)
- For 'Number of bits in a generated key', leave the default value (
2048).
- Under 'Actions', click Generate.
- When prompted, use your mouse (or trackpad) to move your cursor around the blank area under 'Key'; this generates randomness that PuTTYgen uses to generate your key pair.
- When your key pair is generated, PuTTYgen displays the public key in the area under 'Key'. In the 'Key passphrase' and 'Confirm passphrase' text boxes, enter a passphrase to passphrase-protect your private key.If you don't passphrase-protect your private key, anyone with access to your computer will be able to SSH (without being prompted for a passphrase) to your account on any remote system that has the corresponding public key.
- Save your public key:
- Under 'Actions', next to 'Save the generated key', click Save public key.
- Give the file a name (for example,
putty_key), select a location on your computer to store it, and then click Save.
- Save your private key:
- Under 'Actions', next to 'Save the generated key', click Save private key.If you didn't passphrase-protect your private key, the utility will ask whether you're sure you want to save it without a passphrase. Click Yes to proceed or No to go back and create a passphrase for your private key.
- Keep 'Save as type' set to PuTTY Private Key Files (*.ppk), give the file a name (for example,
putty_private_key), select a location on your computer to store it, and then click Save. - If you wish to connect to a remote desktop system such as Research Desktop (RED), click Conversions > Export OpenSSH key, give the file a name (for example,
putty_rsa), select a location on your computer to store it, and then click Save.
- Under 'Actions', next to 'Save the generated key', click Save private key.
- Log into the remote system using your account username and password.
If the remote system does not support password-based authentication, you will need to ask system administrators to add your public key to the
~/.ssh/authorized_keysfile in your account (if your account doesn't have~/.ssh/authorized_keysfile, system administrators can create one for you). Once your public key is added to your account's~/.ssh/authorized_keysfile on the remote system.. - If your account on the remote system doesn't already contain a
~/.ssh/authorized_keysfile, create one; on the command line, enter the following commands:If your account on the remote system already has
~/.ssh/authorized_keys, executing these commands will not damage the existing directory or file. - On your computer, in the PuTTYgen utility, copy the contents of the public key (displayed in the area under 'Key') onto your Clipboard. Then, on the remote system, use your favorite text editor to paste it onto a new line in your
~/.ssh/authorized_keysfile, and then save and close the file. - On your computer, open the Pageant SSH authentication agent. This utility runs in the background, so when it opens, you should see its icon displayed in the Windows notification area.
- In the Windows notification area, right-click on the Pageant icon, select Add Key, navigate to the location where you saved your private key (for example,
putty_private_key.ppk), select the file, and then click Open. - If your private key is passphrase-protected, Pageant will prompt you to enter the passphrase; enter the passphrase for your private key, and then click OK.
If your private key is not passphrase-protected, Pageant will add your private key without prompting you for a passphrase.
Either way, Pageant stores the unencrypted private key in memory for use by PuTTY when you initiate an SSH session to the remote system that has your public key.
- On your computer, open the PuTTY SSH client:
- On the Session screen:
- Under 'Host Name (or IP address)', enter your username coupled with the hostname of the remote server that has your public key; for example:
- Under 'Connection type', make sure SSH is selected.
- In the 'Category' list on the left, navigate to the Auth screen (Connection > SSH > Auth). On the Auth screen, under 'Authentication methods', select Attempt authentication using Pageant.
- Return to the Session screen, and under 'Saved Sessions', enter a name (for example,
Deathstar), and then click Save. - Click Open to connect to your account on the remote system. With Pageant running in the background, PuTTY will retrieve the unencrypted private key automatically from Pageant and use it to authenticate. Because Pageant has your private key's passphrase saved (if applicable), the remote system will place you on the command line in your account without prompting you for the passphrase.
Technically, at this point, the setup is complete. In the future, whenever you log into your Windows desktop, you can run Pageant, add the private key, and then use PuTTY to SSH to any remote resource that has your public key. Alternatively, you can create a shortcut in your WindowsStartupfolder to launch Pageant and load your private key automatically whenever you log into your desktop. For instructions, finish the rest of the following steps. - On the Session screen:
- Open your
Startupfolder. PressWin-r, and in the 'Open' field, typeshell:startup, and then pressEnter. - Right-click inside the
Startupfolder, and then select New and Shortcut. - In the 'Type the location of the item' text box, enter the path to the Pageant executable (
pageant.exe) followed by the path to your private key file (for example,putty_private_key.ppk); enclose both paths in double quotes; for example: - Click Next, and then, in the 'Type a name for this shortcut' text box, enter a name for the shortcut (for example,
PAGEANT). - Click Finish.
The next time you log into your Windows desktop, Pageant will start automatically, load your private key, and (if applicable) prompt you for the passphrase.