- Python Generate Private And Public Keys Florida
- Python Generate Private And Public Keys Free
- Python Generate Private And Public Keys Fl
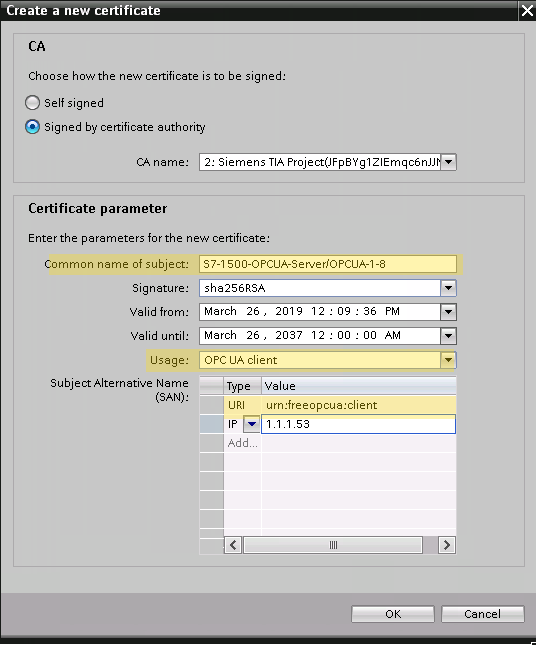
Mar 29, 2016 This tutorial explains how to create a public private keystore for client and server. You can use these keystores to secure communication between client and server. Create Public Private KeyStore for Client and Server. By MemoryNotFound March 29, 2016. We can extract the public key from the keystore using the following command.
- Cryptography with Python Tutorial
- Useful Resources
- Selected Reading
In this chapter, we will focus on step wise implementation of RSA algorithm using Python.
Generating RSA keys
The following steps are involved in generating RSA keys −
Create two large prime numbers namely p and q. The product of these numbers will be called n, where n= p*q
Generate a random number which is relatively prime with (p-1) and (q-1). Let the number be called as e.
Calculate the modular inverse of e. The calculated inverse will be called as d.
Algorithms for generating RSA keys
We need two primary algorithms for generating RSA keys using Python − Cryptomath module and Rabin Miller module.
Cryptomath Module
The source code of cryptomath module which follows all the basic implementation of RSA algorithm is as follows −
RabinMiller Module
The source code of RabinMiller module which follows all the basic implementation of RSA algorithm is as follows −
The complete code for generating RSA keys is as follows −
Output
The public key and private keys are generated and saved in the respective files as shown in the following output.
How to Generate a Public/Private KeyPair for Use With Solaris Secure Shell
Users must generate a public/private key pair when their site implementshost-based authentication or user public-key authentication. For additionaloptions, see the ssh-keygen(1) manpage.
Before You Begin
Determine from your system administrator if host-based authenticationis configured.
Python Generate Private And Public Keys Florida
Start the key generation program.
where -t is the type of algorithm, one of rsa, dsa, or rsa1.
Specify the path to the file that will hold the key.
Bydefault, the file name id_rsa, which represents an RSAv2 key, appears in parentheses. You can select this file by pressing the Return key. Or, you can type an alternative file name.
The file name of the public key is created automatically by appendingthe string .pub to the name of the private key file.
Type a passphrase for using your key.
This passphraseis used for encrypting your private key. A null entry is stronglydiscouraged. Note that the passphrase is not displayed when youtype it in.
Retype the passphrase to confirm it.
Check the results.
Check that the path to the keyfile is correct.
At this point, you have created a public/private key pair.
Choose the appropriate option:
If your administrator has configuredhost-based authentication, you might need to copy the local host's publickey to the remote host.
You can now log in to the remote host.For details, see How to Log In to a Remote Host With Solaris Secure Shell.
Type the command on one line with no backslash.
When you are prompted, supply your login password.
If your site uses user authentication with public keys, populateyour authorized_keys file on the remote host.
Copyright Disclaimer Under Section 107 of the Copyright Act 1976, allowance is made for “fair use” for purposes such as criticism, comment, news reporting, teaching, scholarship, and research.
Copy your public key to the remote host.
Type thecommand on one line with no backslash.
When you are prompted, supply your login password.
Whenthe file is copied, the message “Key copied” is displayed.
(Optional) Reduce the prompting for passphrases.
Then relaunch your browser.You can see an example of the browser’s warning behavior on.When the Not Secure state is shown, the DevTools console shows the message Thispage includes a password or credit card input in a non-secure context. Allow all sites to use key generation in forms chrome. Enable warningsWarnings will be enabled by default for everyone in Chrome 56, slated forrelease in January 2017.To test the upcoming user experience before that time, install the latestbuild.To configure Chrome to show the warning as it will appear in January 2017, openchrome://flags/#mark-non-secure-as and set the Mark non-secure origins asnon-secure option to Display a verbose state when password or credit cardfields are detected on an HTTP page. Eric is a contributor to Web FundamentalsAs,Chrome will soon mark non-secure pages containing password and creditcard input fields as Not Secure in the URL bar.This document is intended to aid Web Developers in updating their sites to avoidthis warning.
For a procedure, see How to Reduce Password Prompts in Solaris Secure Shell. For more information, see the ssh-agent(1) and ssh-add(1) man pages.
Example 19–2 Establishing a v1 RSA Key for a User
Python Generate Private And Public Keys Free
In the following example, the user cancontact hosts that run v1 of the Solaris Secure Shell protocol. To be authenticated by v1hosts, the user creates a v1 key, then copies the public key portion to theremote host.
