- Red Hat Linux Generate Ssh Keyboard
- Red Hat Linux Generate Ssh Key Git Bash
- Generate Ssh Key Ubuntu
- Red Hat Linux Generate Ssh Key Pair
- Mac Generate Ssh Key
Feb 11, 2017 In this video i demonstrated how to generate a ssh key on centos 7. Skip navigation. How to generate an SSH Key on Centos 7 RHEL7 waris. Understanding SSH in Red Hat Enterprise Linux 7. Sep 06, 2019 The minimum effort to generate a key pair involves running the ssh-keygen command. Free Event: Red Hat Summit 2020 Virtual Experience. Attend the Red Hat Summit 2020 virtual experience, April 28-29. When it comes to Linux system troubleshooting, find is my best friend. In order to generate a key, we will use a tool called ssh-keygen.Open Terminal on Linux or Mac, or Git Bash on Windows. Enter the following: ssh-keygen -t rsa -C '[email protected]' After you have entered this command you will be asked where to save the key.
If you interact regularly with SSH commands and remote hosts, you may find that using a key pair instead of passwords can be convenient. Instead of the remote system prompting for a password with each connection, authentication can be automatically negotiated using a public and private key pair.
The private key remains secure on your own workstation, and the public key gets placed in a specific location on each remote system that you access. Your private key may be secured locally with a passphrase. A local caching program such as ssh-agent or gnome-keyring allows you to enter that passphrase periodically, instead of each time you use the key to access a remote system.
Generating a key pair and propagating the public key
Generating your key pair and propagating your public key is simpler than it sounds. Let’s walk through it.
Generating the key
The minimum effort to generate a key pair involves running the ssh-keygen command, and choosing the defaults at all the prompts:
The default location to store the keys is in the ~/.ssh directory, which will be created if it does not exist:
Allowing this command to create the directory also ensures that the owner and permissions are set correctly. Some applications will not use keys if the permissions to the private key are too open.
The file ending in .pub is the public key that needs to be transferred to the remote systems. It is a file containing a single line: The protocol, the key, and an email used as an identifier. Options for the ssh-keygen command allow you to specify a different identifier:
After generating the key pair, the ssh-keygen command also displays the fingerprint and randomart image that are unique to this key. This information can be shared with other people who may need to verify your public key.
Later you can view these with:
The -l option lists the fingerprint, and the -v option adds the ASCII art.
Propagating the public key to a remote system
If password authentication is currently enabled, then the easiest way to transfer the public key to the remote host is with the ssh-copy-id command. If you used the default name for the key all you need to specify is the remote user and host:
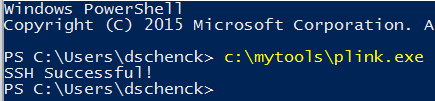
Following the instructions from the output, verify that you can connect using the key pair. If you implemented a passphrase, you will be prompted for the passphrase to use the private key:
.Visual Basic 2008 Express Edition ReviewVisual Basic 2008 Express Edition is a development studio for student and beginner programmers where they can create all kinds of programs for Windows.With this light version of Visual Basic you can use tools that take advantage of the APIs in Windows Vista, that transmit data via the Internet using P2P, or that integrate video and audio in the forms.There's even more. 
Examine the resulting authorized key file. This is where the public key was appended. If the directory or file did not exist, then it was (or they were) created with the correct ownership and permissions. Each line is a single authorized public key:
To revoke access for this key pair, remove the line for the public key.
There are many other options that can be added to this line in the authorized key file to control access. These options are usually used by administrators placing the public keys on a system with restrictions. These restrictions may include where the connection may originate, what command(s) may be run, and even a date indicating when to stop accepting this key. These and more options are listed in the sshd man page.
Changing the passphrase
If you need to change a passphrase on your private key or if you initially set an empty passphrase and want that protection at a later time, use the ssh-keygen command with the -p option:
You can add additional options to specify the key (-f), and the old (-P) or new (-N) passphrases on the command line. Remember that any passwords specified on the command line will be saved in your shell history.
See the ssh-keygen man page for additional options.
Rotating keys
While the public key by itself is meant to be shared, keep in mind that if someone obtains your private key, they can then use that to access all systems that have the public key. These key pairs also do not have a period of validity like GNU Privacy Guard (GPG) keys or public key infrastructure (PKI) certificates.

If you have any reason to suspect that a private key has been stolen or otherwise compromised, you should replace that key pair. The old public key has to be removed from all systems, a new key has to be generated with ssh-keygen, and the new public key has to be transferred to the desired remote systems.
If you are rotating keys as a precaution and without any concern of compromise, you can use the old key pair to authenticate the transfer of the new public key before removing the old key.
Is using empty passphrases ever a good idea?
There are several things to think about when considering an empty passphrase for your SSH private key.
How secure is the private key file?
If you tend to work from multiple client systems and want to either have multiple copies of your key or keep a copy on removable media, then it really is a good idea to have a passphrase on the private key. This practice is in addition to protecting access to the key file with encrypted media.
However, if you have only one copy of the private key and it is kept on a system that is well secured and not shared, then having a passphrase is simply one more level of protection just in case.
Remember that changing the passphrase on one copy does not change the passphrase on other copies. The passphrase is simply locking access to a specific key file.
Why do think you need an empty passphrase?
There are cases for keys with empty passphrases. Some utilities that need to automatically transfer files between systems need a passwordless method to authenticate. The kdump utility, when configured to dump the kernel to a remote system using SSH, is one example.
Another common use is to generate a key pair for a script that is designed to run unattended, such as from a cron job.
How about a middle ground alternative?
By itself, a passphrase-protected private key requires the passphrase to be entered each time the key is used. This setup does not feel like passwordless SSH. However, there are caching mechanisms that allow you to enter the key passphrase once and then use the key over and over without reentering that passphrase.
More Linux resources
OpenSSH comes with an ssh-agent daemon and an ssh-add utility to cache the unlocked private key. The GNOME desktop also has a keyring daemon that stores passwords and secrets but also implements an SSH agent.
The lifetime of the cached key can be configured with each of the agents or when the key is added. In many cases, it defaults to an unlimited lifetime, but the cache is cleared when the user logs out of the system. You will be prompted for the passphrase only once per login session.
If there is a scheduled application that needs to run outside of a user login session, it may be possible to use a secret or other password manager to automate the unlocking of the key. For example, Ansible Tower stores credentials in a secure database. This database includes an SSH private key used to connect to the remote systems (managed nodes), and any passphrases necessary for those private keys. Once those credentials are stored, a job can be scheduled to run a playbook on a regular schedule.
Automating propagation
A centralized identity manager such as FreeIPA can assist with key propagation. Upload the public key to the server as an attribute of a user account, and then propagate it to the hosts in the domain as needed. FreeIPA can also provide additional host-based access control for where a key may be used.
Keys can also be distributed using Ansible modules. The openssh_keypair module uses ssh-keygen to generate keys and the authorized_key module adds and removes SSH authorized keys for particular user accounts.
Wrapping up
SSH key pairs are only one way to automate authentication without passwords. Using the Generic Security Services Application Program Interface (GSSAPI) authentication is also common when trying to reduce the use of passwords on a network with centralized user management. SSH key pairs are the easier option to implement when single sign-on (SSO) is not already available.
Many source code repositories grant access using SSH keys. You can upload a public key to an account in the hosting organization such as the Fedora Account System, GitLab, or GitHub sites and use that key pair to authenticate when pulling and pushing content to repositories.
Free Event: Red Hat Summit 2020 Virtual Experience
Attend the Red Hat Summit 2020 virtual experience, April 28-29.
Related Content
Some sites I interact with use SSH keys for access instead of passwords. As with passwords, I try to make a conscious decision about passphrases, and when to reuse or make new keys.
To manage these keys, I use a combination of command-line options, configuration settings, and passphrase caching agents.
Why use different key pairs?
More Linux resources
I currently have about a half dozen places where I use SSH keys on a regular basis and several other less frequently accessed locations. In particular, I use different key pairs for:
- Each of my consulting clients.
- Lab or testing environments.
- Training classrooms and similar environments that use shared keys.
- Networks I manage where the public key is loaded into an identity management system that propagates it out to the systems I access interactively.
- Each upstream community that allows SSH access, usually to gain write access for source control commits. (Again, the public key is often uploaded to a central site and propagated in an automated manner.)
Of course, I need to keep all of these keys secure. I passphrase protect all (ok, most of) the keys, and am careful about access to the private key files. In addition to the keys used from my workstation, I also have separate keys for any shared applications, plus the keys that need to be uploaded to an automation system such as Ansible Tower.
How does my system decide which key to use?
When I generate an SSH key pair, I get prompted for the name of the public key (identity) file with a default of ~/.ssh/id_rsa. I pick a name that hopefully makes as much sense to future me as it does currently. When I use a client command such as ssh or scp, the utility selects a file based on command-line options, a per-host basis in the configuration file, or program defaults:
The ssh man page not only describes the -i option, but also has a section titled AUTHENTICATION which further explains the steps used to determine which key or other method is used.
Command-line options
There are a few options I use on the command line during setup, or for verification and then later in the configuration file for future use. The -i option specifies the key to use and works the same with all of the SSH client utilities, including the ssh, ssh-copy-id, and scp commands:
This option can be given muliple times to limit which keys to try, if you know it is one of a handful of keys, but I usually only need to specify the exact key.
I also use a handful of other options specified with -o. These options are described in the ssh_config man page. The IdentityFile SSH option can be used instead of -i. The following command has the same result as the one above:
Other options I use include:
PreferredAuthenticationsspecifies the order of methods to try. The default generally has five to six options listed with Kerberos first, keys in the middle, and password last. If I know I need to be prompted for a password, such as when copying a new public key to a host, I use-o PreferredAuthentications=password.PasswordAuthenticationdefaults toyesso that if other methods fail, the user will see a password prompt. I sometimes disable this setting to ensure that I am authenticating with a method other than SSH password authentication. If I see a prompt, I know it is a passphrase or Kerberos prompt. I only need to specifyPasswordAuthentication=yesif I am trying to override a locally customized configuration file.PubkeyAuthenticationdefaults toyesso that key authentication is attempted. I may set this option to no if I know I need to be prompted for a password, such as to add or replace a key usingssh-copy-id.IdentitiesOnlydefaults tono, but when set toyes, tells SSH to use only the identity specified on the command line or in the configuration file. The client will not try other identities, even if offered byssh-agentor a PK11 provider.
Common authentication error
There is a limit on attempts before the SSH server will fail the authentication. When I try to place a key on a new system, I often get a Received disconnect from x.x.x.x port 22:2: Too many authentication failures error message, which means that the client attempted to authenticate with each method and each key and was ultimately disconnected from the server before getting to the final method of prompting for a password.
In the sshd_config file, you can configure MaxAuthTries. It defaults to six. If I have just key and password authentication methods in use, and I have more than five keys, each key is checked in turn until I'm disconnected from the server before I get a chance to enter a password. I don’t always have access to the server-side configuration. Even if I did, I would not change this setting just for the few users that have such a large collection of keys.
When I know I need password authentication, I make use of PubkeyAuthentication=no or PrefferedAuthentication=password to make sure I get prompted for the password. If I have a particular key to use, I can specify the key and set IdentiesOnly=yes so that only that key is tried:
Configuration file Host entries
To avoid repetitive and lengthy command-line options, I maintain a local configuration file that sets the identity and other options for each destination. As a user, I configure a ~/.ssh/config file. I start by copying the sample from the /etc/ssh directory and then I make use of the ssh_config man page for additional possibilities:
For example, I might create a Host section for each destination. Each Host entry supports multiple destinations, as well as wildcards for pattern matching. The ssh_config man page shows many examples, but here’s a particularly useful one for Fedora users:
If you have a different username on different systems, you can add the User option to specify which one. When I connect to one of the hosts listed above, I can just use ssh host instead of ssh user@host, and the correct username will be passed from the configuration file, thanks to:
You can also add one or more IdentityFile lines for keys used at these sites:
Red Hat Linux Generate Ssh Keyboard
Then, add any other options for managing the connection. This includes options to enable or disable authentication methods as well as destination ports, environment settings, and proxy commands. You might ultimately end up with:
This section of your ~./ssh/config file might end up looking something like this:
Red Hat Linux Generate Ssh Key Git Bash
A final word on lost keys and key rotation
With multiple keys, I need to determine if all keys were compromised, or if only a single key needs to be rotated. A theft of my laptop would be all keys. If I copy a single key to a new client system and forget to remove it, then I only worry about that one key. Which is exactly why I use different keys for lab testing or any situation where I may need to share a key. My client configuration files then make it easy for me to use a variety of keys on a daily basis.
Generate Ssh Key Ubuntu
Free Event: Red Hat Summit 2020 Virtual Experience
Red Hat Linux Generate Ssh Key Pair
Attend the Red Hat Summit 2020 virtual experience, April 28-29.