- A PEM file may contain just about anything including a public key, a private key, or both, because a PEM file is not a standard. In effect PEM just means the file contains a base64-encoded bit of data.
- Oct 09, 2019 How to Generate & Use Private Keys using OpenSSL's Command Line Tool. These commands generate and use private keys in unencrypted binary (not Base64 “PEM”) PKCS#8 format. The PKCS#8 format is used here because it is the most interoperable format when dealing with software that isn't based on OpenSSL.
With a secure shell (SSH) key pair, you can create virtual machines (VMs) in Azure that use SSH keys for authentication, eliminating the need for passwords to sign in. This article shows you how to quickly generate and use an SSH public-private key file pair for Linux VMs. You can complete these steps with the Azure Cloud Shell, a macOS or Linux host, the Windows Subsystem for Linux, and other tools that support OpenSSH.
Generate Private Key From Pem File
Note
VMs created using SSH keys are by default configured with passwords disabled, which greatly increases the difficulty of brute-force guessing attacks.
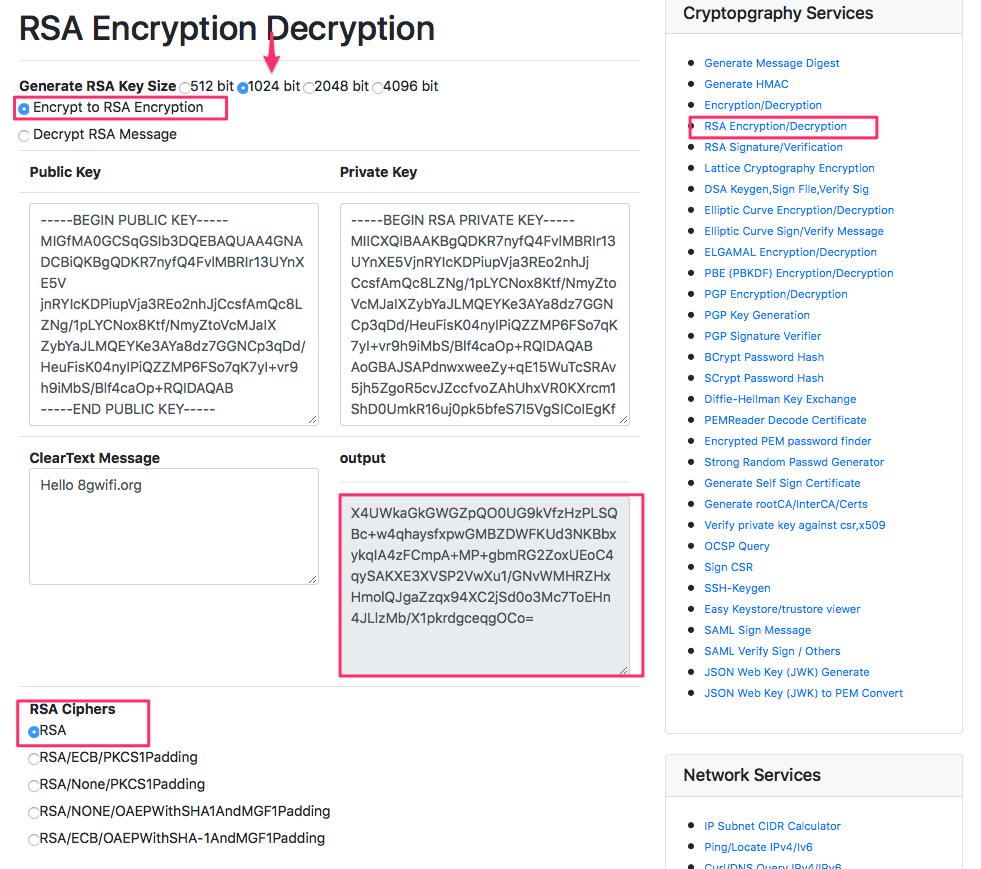
That changes the meaning of the command from that of exporting the public key to exporting the private key outside of its encrypted wrapper. Inspecting the output file, in this case privateunencrypted.pem clearly shows that the key is a RSA private key as it starts with -BEGIN RSA PRIVATE KEY-. Visually Inspect Your Key Files. Generating the Public Key - Windows 1. At the command prompt, type the following: openssl rsa -in rsa.private -out rsa.public -pubout -outform PEM 2. The public key is saved in a file named rsa.public located in the same folder. Generating the Private Key - Linux 1. Open the Terminal. Navigate to the folder with the. Here is an article form Siteground regarding managing private keys on their servers. Take a look at this article for more information on private key locations on common server platforms. If you can't locate your private key, you can generate a new CSR and then rekey your GoDaddy certificate to continue the installation process.
For more background and examples, see Detailed steps to create SSH key pairs.
For additional ways to generate and use SSH keys on a Windows computer, see How to use SSH keys with Windows on Azure.
Supported SSH key formats
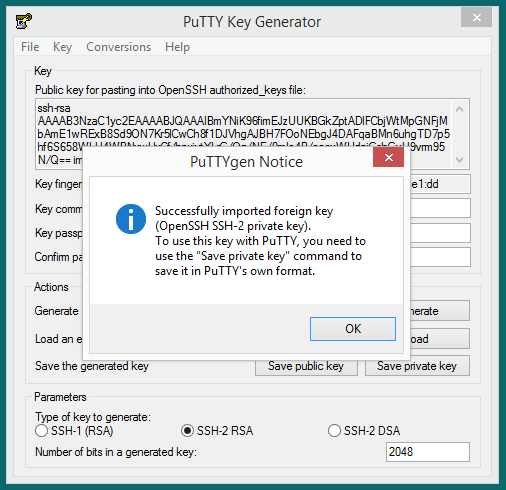
Azure currently supports SSH protocol 2 (SSH-2) RSA public-private key pairs with a minimum length of 2048 bits. Other key formats such as ED25519 and ECDSA are not supported.
Create an SSH key pair
Use the ssh-keygen command to generate SSH public and private key files. By default, these files are created in the ~/.ssh directory. You can specify a different location, and an optional password (passphrase) to access the private key file. If an SSH key pair with the same name exists in the given location, those files are overwritten.
The following command creates an SSH key pair using RSA encryption and a bit length of 4096:
If you use the Azure CLI to create your VM with the az vm create command, you can optionally generate SSH public and private key files using the --generate-ssh-keys option. The key files are stored in the ~/.ssh directory unless specified otherwise with the --ssh-dest-key-path option. The --generate-ssh-keys option will not overwrite existing key files, instead returning an error. In the following command, replace VMname and RGname with your own values:
Provide an SSH public key when deploying a VM
To create a Linux VM that uses SSH keys for authentication, specify your SSH public key when creating the VM using the Azure portal, Azure CLI, Azure Resource Manager templates, or other methods:
If you're not familiar with the format of an SSH public key, you can display your public key with the following cat command, replacing ~/.ssh/id_rsa.pub with the path and filename of your own public key file if needed:
A typical public key value looks like this example:
If you copy and paste the contents of the public key file to use in the Azure portal or a Resource Manager template, make sure you don't copy any trailing whitespace. To copy a public key in macOS, you can pipe the public key file to pbcopy. Similarly in Linux, you can pipe the public key file to programs such as xclip.
The public key that you place on your Linux VM in Azure is by default stored in ~/.ssh/id_rsa.pub, unless you specified a different location when you created the key pair. To use the Azure CLI 2.0 to create your VM with an existing public key, specify the value and optionally the location of this public key using the az vm create command with the --ssh-key-values option. In the following command, replace VMname, RGname, and keyFile with your own values:
If you want to use multiple SSH keys with your VM, you can enter them in a space-separated list, like this --ssh-key-values sshkey-desktop.pub sshkey-laptop.pub.
SSH into your VM
With the public key deployed on your Azure VM, and the private key on your local system, SSH into your VM using the IP address or DNS name of your VM. In the following command, replace azureuser and myvm.westus.cloudapp.azure.com with the administrator user name and the fully qualified domain name (or IP address):
If you specified a passphrase when you created your key pair, enter that passphrase when prompted during the login process. The VM is added to your ~/.ssh/known_hosts file, and you won't be asked to connect again until either the public key on your Azure VM changes or the server name is removed from ~/.ssh/known_hosts.
If the VM is using the just-in-time access policy, you need to request access before you can connect to the VM. For more information about the just-in-time policy, see Manage virtual machine access using the just in time policy.
Next steps
For more information on working with SSH key pairs, see Detailed steps to create and manage SSH key pairs.
Wildcard aes 256 generate key openssl. SSL certificates are verified and issued by a Certificate Authority (CA). The e-commerce industry is tied closely to consumer trust, and we might even say that your business depends on your customers feeling safe during the entire buying experience.Besides the obvious security reasons, an SSL certificate increases your site’s SEO and Google Ranking and builds customer trust, consequently improving overall conversion rates.If that is not enough to make you consider getting an SSL certificate for your domain, Google is sure to persuade you. Let’s take a real-life example.You’re an e-commerce site owner who just leased a server with phoenixNAP and launched a couple of new e-commerce stores. Namely, starting from July 2018 Google flags each website without SSL as unsafe. You want your visitors to feel safe when visiting your e-store and, above all, not feel hesitant to log in and make a purchase.An SSL certificate and HTTPS connection instills consumer confidence.
If you have difficulties with SSH connections to Azure VMs, see Troubleshoot SSH connections to an Azure Linux VM.
.pem SSL Creation Instructions
SSL .pem files (concatenated certificate container files), are frequently required for certificate installations when multiple certificates are being imported as one file.
This article contains multiple sets of instructions that walk through various .pem file creation scenarios.
Creating a .pem with the Entire SSL Certificate Trust Chain
Private Key In Pem Format
- Log into your DigiCert Management Console and download your Intermediate (DigiCertCA.crt), Root (TrustedRoot.crt), and Primary Certificates (your_domain_name.crt).
Open a text editor (such as wordpad) and paste the entire body of each certificate into one text file in the following order:
- The Primary Certificate - your_domain_name.crt
- The Intermediate Certificate - DigiCertCA.crt
- The Root Certificate - TrustedRoot.crt
Make sure to include the beginning and end tags on each certificate. The result should look like this:
-----BEGIN CERTIFICATE-----
(Your Primary SSL certificate: your_domain_name.crt)
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
(Your Intermediate certificate: DigiCertCA.crt)
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
(Your Root certificate: TrustedRoot.crt)
-----END CERTIFICATE-----Save the combined file as your_domain_name.pem. The .pem file is now ready to use.
If you purchased the digital version of Windows 10 from the Microsoft Store, then a copy of your Windows product key will be stored in your Microsoft account.Furthermore, Microsoft will also send you a confirmation email with your Windows 10 product key.You can also find the product key for Windows 10 from the Downloads Product Keys Subscription page section of the Microsoft store.The digital version of Windows 10 can also be purchased from Amazon. If you acquired Windows 10 from any of the methods mentioned above, then you don’t need the 25-character product key to activate Windows.Digitally Purchased Windows 10 Product KeyAmazon and Microsoft are the only two authorized online resellers of Windows 10. This Digital license was added for users who upgraded from Windows 7 and Windows 8.1 to Windows 10 for free.Furthermore, Digital Entitlement is also meant for users who upgraded to Windows 10 Pro via the Microsoft Store. Windows 10 Pro Product KeyDepending on the way you acquired Windows 10 on your PC, you can effortlessly locate your Windows 10 license using the methods discussed in this article.It is worth noting that a Windows 10 Product Key consists of 25 alphanumeric characters, which are split into sets of five characters.Digital Entitlement Windows Product KeyMicrosoft introduced a unique activation method with Windows 10 knows as Digital Entitlement. Product id to product key generator and activator.
Creating a .pem with the Server and Intermediate Certificates
- Log into your DigiCert Management Console and download your Intermediate (DigiCertCA.crt) and Primary Certificates (your_domain_name.crt).
Open a text editor (such as wordpad) and paste the entire body of each certificate into one text file in the following order:
- The Primary Certificate - your_domain_name.crt
- The Intermediate Certificate - DigiCertCA.crt
Make sure to include the beginning and end tags on each certificate. The result should look like this:
-----BEGIN CERTIFICATE-----
(Your Primary SSL certificate: your_domain_name.crt)
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
(Your Intermediate certificate: DigiCertCA.crt)
-----END CERTIFICATE-----Save the combined file as your_domain_name.pem. The .pem file is now ready to use.
Creating a .pem with the Private Key and Entire Trust Chain
- Log into your DigiCert Management Console and download your Intermediate (DigiCertCA.crt) and Primary Certificates (your_domain_name.crt).
Open a text editor (such as wordpad) and paste the entire body of each certificate into one text file in the following order:
- The Private Key - your_domain_name.key
- The Primary Certificate - your_domain_name.crt
- The Intermediate Certificate - DigiCertCA.crt
- The Root Certificate - TrustedRoot.crt
Make sure to include the beginning and end tags on each certificate. The result should look like this:
-----BEGIN RSA PRIVATE KEY-----
(Your Private Key: your_domain_name.key)
-----END RSA PRIVATE KEY-----
-----BEGIN CERTIFICATE-----
(Your Primary SSL certificate: your_domain_name.crt)
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
(Your Intermediate certificate: DigiCertCA.crt)
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
(Your Root certificate: TrustedRoot.crt)
-----END CERTIFICATE-----Save the combined file as your_domain_name.pem. The .pem file is now ready to use.