- Generate Rsa Key Linux 2048
- Generate Rsa Keys In Linux Version
- Generate Rsa Keys In Linux Windows 7
- How To Generate Rsa Public And Private Keys In Linux
- Generate Rsa Key Linux Openssl
Several tools exist to generate SSH public/private key pairs. The following sections show how to generate an SSH key pair on UNIX, UNIX-like and Windows platforms.
Generating an SSH Key Pair on UNIX and UNIX-Like Platforms Using the ssh-keygen Utility
UNIX and UNIX-like platforms (including Solaris and Linux) include the ssh-keygen utility to generate SSH key pairs.
Apr 02, 2019 Installation of SSH Keys on Linux - A Step-By-Step Guide. Outlined below is a step-by-step guide detailing the process of installing SSH Keys on a Linux server: Step One: Creation of the RSA Key Pair. The first step in the installation process is to create the key pair on the client machine, which would, more often than not, be your own system. Generate a 2048 bit RSA Key. You can generate a public and private RSA key pair like this: openssl genrsa -des3 -out private.pem 2048. That generates a 2048-bit RSA key pair, encrypts them with a password you provide and writes them to a file. You need to next extract the public key file.
- Navigate to your home directory:
- Run the ssh-keygen utility, providing as
filenameyour choice of file name for the private key:The ssh-keygen utility prompts you for a passphrase for the private key.
- Enter a passphrase for the private key, or press Enter to create a private key without a passphrase:
Note:
While a passphrase is not required, you should specify one as a security measure to protect the private key from unauthorized use. When you specify a passphrase, a user must enter the passphrase every time the private key is used.
The ssh-keygen utility prompts you to enter the passphrase again.
- Enter the passphrase again, or press Enter again to continue creating a private key without a passphrase:
- The ssh-keygen utility displays a message indicating that the private key has been saved as
filenameand the public key has been saved asfilename.pub. It also displays information about the key fingerprint and randomart image.
Generating an SSH Key Pair on Windows Using the PuTTYgen Program
The PuTTYgen program is part of PuTTY, an open source networking client for the Windows platform.
- Download and install PuTTY or PuTTYgen.
To download PuTTY or PuTTYgen, go to http://www.putty.org/ and click the You can download PuTTY here link.
- Run the PuTTYgen program.
- Set the Type of key to generate option to SSH-2 RSA.
- In the Number of bits in a generated key box, enter 2048.
- Click Generate to generate a public/private key pair.
As the key is being generated, move the mouse around the blank area as directed.
- (Optional) Enter a passphrase for the private key in the Key passphrase box and reenter it in the Confirm passphrase box.
Note:
While a passphrase is not required, you should specify one as a security measure to protect the private key from unauthorized use. When you specify a passphrase, a user must enter the passphrase every time the private key is used.
- Click Save private key to save the private key to a file. To adhere to file-naming conventions, you should give the private key file an extension of
.ppk(PuTTY private key).Note:
The.ppkfile extension indicates that the private key is in PuTTY's proprietary format. You must use a key of this format when using PuTTY as your SSH client. It cannot be used with other SSH client tools. Refer to the PuTTY documentation to convert a private key in this format to a different format. - Select all of the characters in the Public key for pasting into OpenSSH authorized_keys file box.
Make sure you select all the characters, not just the ones you can see in the narrow window. If a scroll bar is next to the characters, you aren't seeing all the characters.
- Right-click somewhere in the selected text and select Copy from the menu.
- Open a text editor and paste the characters, just as you copied them. Start at the first character in the text editor, and do not insert any line breaks.
- Save the text file in the same folder where you saved the private key, using the
.pubextension to indicate that the file contains a public key. - If you or others are going to use an SSH client that requires the OpenSSH format for private keys (such as the
sshutility on Linux), export the private key:- On the Conversions menu, choose Export OpenSSH key.
- Save the private key in OpenSSH format in the same folder where you saved the private key in
.ppkformat, using an extension such as.opensshto indicate the file's content.
This page explains a public key and shows you how to set up SSH keys on a Linux or Unix-like server. I am assuming that you are using Linux or Unix-like server and client with the following software:
- OpenSSH SSHD server
- OpenSSH ssh client and friends on Linux (Ubuntu, Debian, {Free,Open,Net}BSD, RHEL, CentOS, MacOS/OSX, AIX, HP-UX and co).
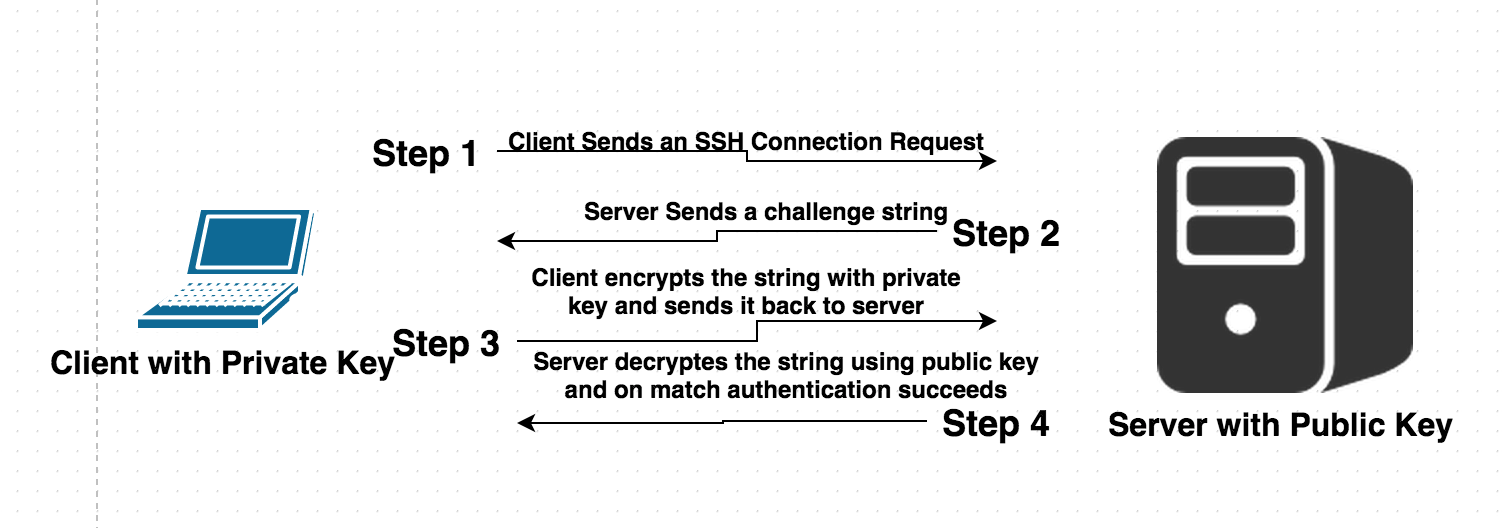
What is a public key authentication?
OpenSSH server supports various authentication schema. The two most popular are as follows:
- Passwords based authentication
- Public key based authentication. It is an alternative security method to using passwords. This method is recommended on a VPS, cloud, dedicated or even home based server.
How to set up SSH keys
Steps to setup secure ssh keys:
- Create the ssh key pair using ssh-keygen command.
- Copy and install the public ssh key using ssh-copy-id command on a Linux or Unix server.
- Add yourself to sudo or wheel group admin account.
- Disable the password login for root account.
- Test your password less ssh keys login using ssh user@server-name command.
Let us see all steps in details.
How do I set up public key authentication?
You must generate both a public and a private key pair. For example:
Where,
- server1.cyberciti.biz – You store your public key on the remote hosts and you have an accounts on this Linux/Unix based server.
- client1.cyberciti.biz – Your private key stays on the desktop/laptop/ computer (or local server) you use to connect to server1.cyberciti.biz server. Do not share or give your private file to anyone.
In public key based method you can log into remote hosts and server, and transfer files to them, without using your account passwords. Feel free to replace server1.cyberciti.biz and client1.cyberciti.biz names with your actual setup. Enough talk, let’s set up public key authentication. Open the Terminal and type following commands if .ssh directory does not exists:
1: Create the key pair
On the computer (such as client1.cyberciti.biz), generate a key pair for the protocol.
Sample outputs:
You need to set the Key Pair location and name. I recommend you use the default location if you do not yet have another key there, for example: $HOME/.ssh/id_rsa. You will be prompted to supply a passphrase (password) for your private key. I suggest that you setup a passphrase when prompted. You should see two new files in $HOME/.ssh/ directory:
Generate Rsa Key Linux 2048
- $HOME/.ssh/id_rsa– contains your private key.
- $HOME/.ssh/id_rsa.pub – contain your public key.
Optional syntax for advance users
The following syntax specifies the 4096 of bits in the RSA key to creation (default 2048):$ ssh-keygen -t rsa -b 4096 -f ~/.ssh/vps-cloud.web-server.key -C 'My web-server key'
Where,
- -t rsa : Specifies the type of key to create. The possible values are “rsa1” for protocol version 1 and “dsa”, “ecdsa”, “ed25519”, or “rsa” for protocol version 2.
- -b 4096 : Specifies the number of bits in the key to create
- -f ~/.ssh/vps-cloud.web-server.key : Specifies the filename of the key file.
- -C 'My web-server key' : Set a new comment.
2: Install the public key in remote server
Use scp or ssh-copy-id command to copy your public key file (e.g., $HOME/.ssh/id_rsa.pub) to your account on the remote server/host (e.g., [email protected]). To do so, enter the following command on your client1.cyberciti.biz:
OR just copy the public key in remote server as authorized_keys in ~/.ssh/ directory:
A note about appending the public key in remote server
On some system ssh-copy-id command may not be installed, so use the following commands (when prompted provide the password for remote user account called vivek) to install and append the public key:
3: Test it (type command on client1.cyberciti.biz)
The syntax is as follows for the ssh command: Uplay cd key generator download.
 @Buscar웃SD, it's possible to get a recovery key because your account is enabled for FileVault 2 and is associated with a key that can unlock the encryption. An account which is not enabled for FileVault would not be able to generate a new recovery key because its password would not be associated with a key which can unlock the encryption. Issuing a New FileVault 2 Recovery Key. Log in to the JSS with a web browser. Click Computers at the top of the page. Click Policies. On a smartphone or iPod touch, this option is in the pop-up menu. Use the General payload to configure basic settings for the policy, including the trigger and execution frequency.
@Buscar웃SD, it's possible to get a recovery key because your account is enabled for FileVault 2 and is associated with a key that can unlock the encryption. An account which is not enabled for FileVault would not be able to generate a new recovery key because its password would not be associated with a key which can unlock the encryption. Issuing a New FileVault 2 Recovery Key. Log in to the JSS with a web browser. Click Computers at the top of the page. Click Policies. On a smartphone or iPod touch, this option is in the pop-up menu. Use the General payload to configure basic settings for the policy, including the trigger and execution frequency.
Or copy a text file called foo.txt:
You will be prompted for a passphrase. To get rid of passphrase whenever you log in the remote host, try ssh-agent and ssh-add commands.
What are ssh-agent and ssh-add, and how do I use them?
To get rid of a passphrase for the current session, add a passphrase to ssh-agent and you will not be prompted for it when using ssh or scp/sftp/rsync to connect to hosts with your public key. The syntax is as follows:
Type the ssh-add command to prompt the user for a private key passphrase and adds it to the list maintained by ssh-agent command:
Enter your private key passphrase. Now try again to log into [email protected] and you will not be prompted for a password:
One can list public key parameters of all identities with the -L option:ssh-add -L
Deleting all private keys from the ssh-agent can be done with the -D option as follows:ssh-add -D
When you log out kill the ssh agent, run:kill $SSH_AGENT_PID
You can also add something like the below to your shell startup to kill ssh-agent at logout:trap 'kill $SSH_AGENT_PID' 0
4: Disable the password based login on a server
Login to your server, type:
Edit /etc/ssh/sshd_config on server1.cyberciti.biz using a text editor such as nano or vim:
Warning: Make sure you add yourself to sudoers files. Otherwise you will not able to login as root later on. See “How To Add, Delete, and Grant Sudo Privileges to Users on a FreeBSD Server” for more info.
$ sudo vim /etc/ssh/sshd_config
OR directly jump to PermitRootLogin line using a vim text editor:$ sudo vim +/PermitRootLogin /etc/ssh/sshd_config
Find PermitRootLogin and set it as follows:
Save and close the file. I am going to add a user named vivek to sudoers on Ubuntu Linux:# adduser vivek
Finally, reload/restart the sshd server, type command as per your Linux/Unix version:
5: How to add or replace a passphrase for an existing private key?
To to change your passphrase type the following command:ssh-keygen -p
6: How do I backup an existing private/public key?
Just copy files to your backup server or external USB pen/hard drive:
How do I protect my ssh keys?
Generate Rsa Keys In Linux Version
- Always use a strong passphrase.
- Do not share your private keys anywhere online or store in insecure cloud storage.
- Restrict privileges of the account.
Generate Rsa Keys In Linux Windows 7
How do I create and setup an OpenSSH config file to create shortcuts for servers I frequently access?
See how to create and use an OpenSSH ssh_config file for more info.
Conclusion
This page explained how to set up ssh keys for authentication purposes. For more info see the following resources:
- Man pages – ssh-keygen(1)
- OpenSSH project homepage here.
How To Generate Rsa Public And Private Keys In Linux
And, there you have it, ssh set up with public key based authentication for Linux or Unix-like systems.
Generate Rsa Key Linux Openssl
ADVERTISEMENTS