- Mac Os Generate Public Ssh Keyboard
- Mac Get Ssh Key
- Generate Public Ssh Key
- How To Generate Public Ssh Key Mac
You generate an SSH key through macOS by using the Terminal application. Once you upload a valid public SSH key, the Triton Compute Service uses SmartLogin to copy the public key to any new SmartMachine you provision.
Joyent recommends RSA keys because the node-manta CLI programs work with RSA keys both locally and with the ssh agent. DSA keys will work only if the private key is on the same system as the CLI, and not password-protected.
About Terminal
Run it on your local computer to generate a 2048-bit RSA key pair, which is fine for most uses. Ssh-keygen The utility prompts you to select a location for the keys. By default, the keys are stored in the /.ssh directory with the filenames idrsa for the private key and idrsa.pub for the public key. Creating a SSH Public Key on OSX¶. You generate an SSH key through Mac OS X by using the Terminal application. Once you upload a valid public SSH key, Gerrit can authenticate you based on this key.
Nov 10, 2011 How to Generate A Public/Private SSH Key Linux By Damien – Posted on Nov 10, 2011 Nov 18, 2011 in Linux If you are using SSH frequently to connect to a remote host, one of the way to secure the connection is to use a public/private SSH key so no password is transmitted over the network and it can prevent against brute force attack.
Terminal is the terminal emulator which provides a text-based command line interface to the Unix shell of macOS.
To open the macOS Terminal, follow these steps:
- In Finder, choose Utilities from the Applications folder.
- Find Terminal in the Utilities listw.
- Open Terminal.
The Terminal window opens with the commandline prompt displaying the name of your machine and your username.
Generating Public and Private Keys in GitHub Now that I am sure I have no keys associated with my remote account let’s go ahead and use SSH for authentication. For this, we generate two types of keys. GitHub authentication is embedded in Unity, including 2FA. And with a click of a button, you can quickly initialize your game’s repository. Use the GitHub for Unity Extension. World of warcraft authentication key. Feb 26, 2020 The Firebase Auth Unity Sample demonstrates user authentication and user profile operations using Firebase Authentication with the Firebase Unity SDK. Unity 5.3 or higher. Xcode 10.3 or higher (when developing for iOS). Android SDK (when developing for Android). Building the Sample iOS. Register your iOS app with Firebase. 16 rows Oct 18, 2019 GitHub is home to over 40 million developers working together to host.
Generating an SSH key
An SSH key consists of a pair of files. One is the private key, which should never be shared with anyone. The other is the public key. The other file is a public key which allows you to log into the containers and VMs you provision. When you generate the keys, you will use ssh-keygen to store the keys in a safe location so you can bypass the login prompt when connecting to your instances.
To generate SSH keys in macOS, follow these steps:
Enter the following command in the Terminal window.
This starts the key generation process. When you execute this command, the
ssh-keygenutility prompts you to indicate where to store the key.Press the ENTER key to accept the default location. The
ssh-keygenutility prompts you for a passphrase.- Type in a passphrase. You can also hit the ENTER key to accept the default (no passphrase). However, this is not recommended.
You will need to enter the passphrase a second time to continue.
After you confirm the passphrase, the system generates the key pair.
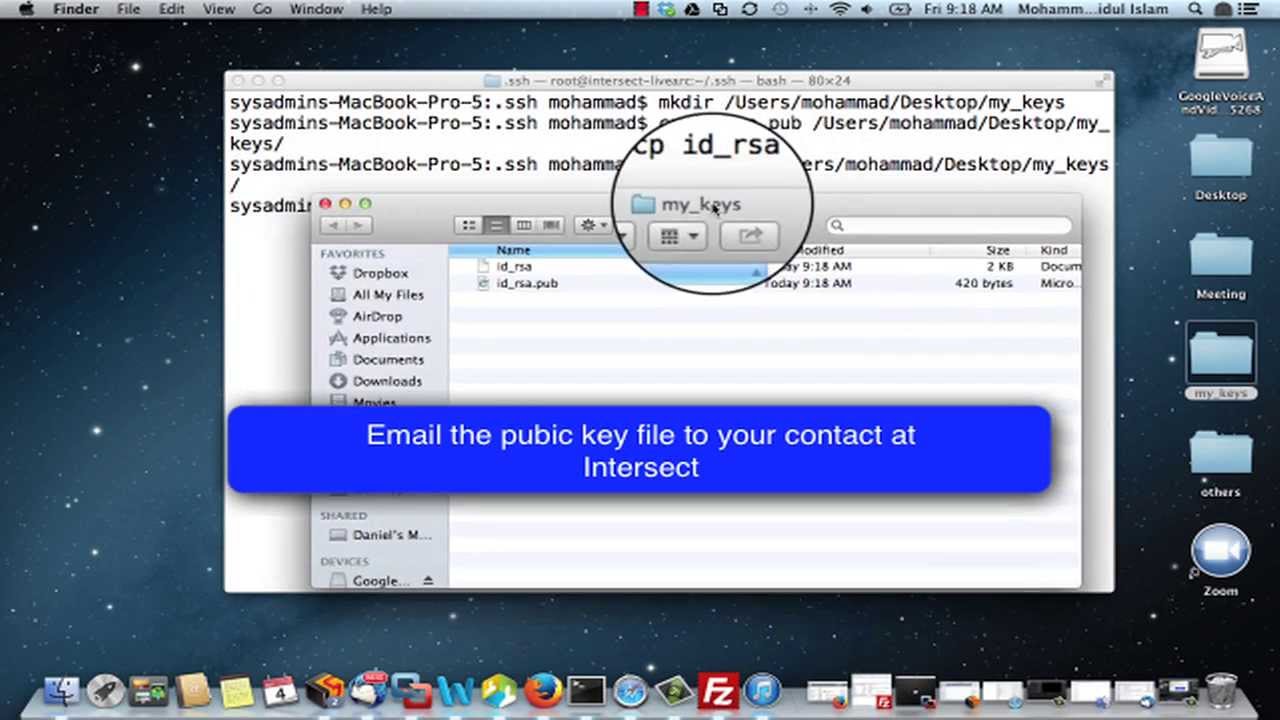
Your private key is saved to the id_rsa file in the .ssh directory and is used to verify the public key you use belongs to the same Triton Compute Service account.
| Never share your private key with anyone! |
|---|
Your public key is saved to the id_rsa.pub;file and is the key you upload to your Triton Compute Service account. You can save this key to the clipboard by running this:
Importing your SSH key
Now you must import the copied SSH key to the portal.
- After you copy the SSH key to the clipboard, return to your account page.
- Choose to Import Public Key and paste your SSH key into the Public Key field.
- In the Key Name field, provide a name for the key. Note: although providing a key name is optional, it is a best practice for ease of managing multiple SSH keys.
- Add the key. It will now appear in your table of keys under SSH.
Troubleshooting
You may see a password prompt like this:
This is because:
- You did not enter the correct passphrase.
- The private key on your Macintosh (
id_rsa) does not match the public key stored with your Triton Compute Service account. - The public key was not entered correctly in your Triton account.
What are my next steps?
Right in the portal, you can easily create Docker containers, infrastructure containers, and hardware virtual machines.
In order to use the Terminal to create instances, set up triton and CloudAPI as well as the triton-docker commandline tool.
This guide will demonstrate the steps required to encrypt and decrypt files using OpenSSL on Mac OS X. The working assumption is that by demonstrating how to encrypt a file with your own public key, you'll also be able to encrypt a file you plan to send to somebody else using their private key, though you may wish to use this approach to keep archived data safe from prying eyes.
Too Long, Didn't Read
Assuming you've already done the setup described later in this document, that id_rsa.pub.pcks8 is the public key you want to use, that id_rsa is the private key the recipient will use, and secret.txt is the data you want to transmit…
Encrypting
Decrypting
Using Passwords
OpenSSL makes it easy to encrypt/decrypt files using a passphrase. Unfortunately, pass phrases are usually 'terrible' and difficult to manage and distribute securely.
To Encrypt a File
Mac Os Generate Public Ssh Keyboard
You can add -base64 if you expect the context of the text may be subject to being 'visible' to people (e.g., you're printing the message on a pbulic forum). If you do, you'll need to add it to the decoding step as well. You can choose from several cypers but aes-256-cbc is reasonably fast, strong, and widely supported. Base64 will increase the size of the encrypted file by approximately 30%
To Decrypt a File
You will need to provide the same password used to encrypt the file. All that changes between the encrypt and decrypt phases is the input/output file and the addition of the -d flag. If you pass an incorrect password or cypher then an error will be displayed.
Encrypting Files Using your RSA keys
RSA encryption can only work with very short sections of data (e.g. an SHA1 hash of a file, or a password) and cannot be used to encrypt a large file. The solution is to generate a strong random password, use that password to encrypt the file with AES-256 in CBC mode (as above), then encrypt that password with a public RSA key. The encrypted password will only decrypt with a matching public key, and the encrypted file will require the unique password encrypted in the by the RSA key.
Replace OpenSSL
The copy of OpenSSL bundled with Mac OS X has several issues. Mac OS X 10.7 and earlier are not PCI compliant. It is best to replace it. See here for details: http://www.dctrwatson.com/2013/07/how-to-update-openssh-on-mac-os-x/
Generate Your Private/Public Key-pair
By default your private key will be stored in
- ~/.ssh/id_rsa : This is your private key and it must be kept secret
- ~/.ssh/id_rsa.pub : This is your public key, you can share it (for example) with servers as an authorized key for your account.You can change the location of where you store your keys, but this location is typical. Typically you want to ensure the private key is chmod 600, andd the public key is chmod 644.
Generate a PKCS8 Version of Your Public Key
The default format of id_rsa.pub isn't particularly friendly. If you are going to public your key (for example) on your website so that other people can verify the authorship of files attributed to you then you'll want to distribute it in another format. I find it useful to keep a copy in my .ssh folder so I don't have to re-generate it, but you can store it anywhere you like.
Generate a One-Time-Use Password to Encrypt the File
The passwords used to encrypt files should be reasonably long 32+ characters, random, and never used twice. To do this we'll generate a random password which we will use to encrypt the file.
This will generate 192 bytes of random data which we will use as a key. If you think a person may need to view the contents of the key (e.g., they're going to display it on a terminal or copy/paste it between computers) then you should consider base-64 encoding it, however:
Mac Get Ssh Key
- The password will become approximately 30% longer (and there is a limit to the length of data we can RSA-encrypt using your public key
- The password will be 'padded' with '=' characters if it's not a multiple of 4 bytes.
Generate Public Ssh Key
A Note on Long Passwords
There is a limit to the maximum length of a message that can be encrypted using RSA public key encryption. If you want to use very long keys then you'll have to split it into several short messages, encrypt them independently, and then concatinate them into a single long string. Decrypting the password will require reversing the technique: splitting the file into smaller chuncks, decrypting them independently, and then concatinating those into the original password key file.
Encrypt the File Using the Generated Key
Now that you have a good random password, you can use that to AES encrypt a file as seen in the 'with passwords' section
Decrypting the file works the same way as the 'with passwords' section, except you'll have to pass the key.
Encrypt the Key Used to Encrypt the File
We used fast symetric encryption with a very strong password to encrypt the file to avoid limitations in how we can use asymetric encryption. Finally, we'll use asymetric encryption to encrypt the password. This solves the problem of 'how do I safely transmit the password for the encrypted file' problem. You can encrypt is using the recipients public key and they can decode it using their private key. Encrypt the password using a public key:
The recipient can decode the password using a matching private key:
Package the Encrypted File and Key
There are a number of ways to do this step, but typically you'll want just a single file you can send to the recipent to make transfer less of a pain. I'd recommend just making a tarball and delivering it through normal methods (email, sftp, dropbox, whatever). Though a secure method of exchange is obviously preferable, if you have to make the data public it should still be resistent to attempts to recover the information.
The file can be extracted in the usual way:
How To Generate Public Ssh Key Mac
You may want to securely delete the unecrypted keyfile as the recipient will be able to decode it using their private key and you already have the unencrypted data.