- Rhel 7 Generate Ssh Host Keys Download
- Rhel 7 Generate Ssh Host Keys Code
- Rhel 7 Generate Ssh Host Keys Free
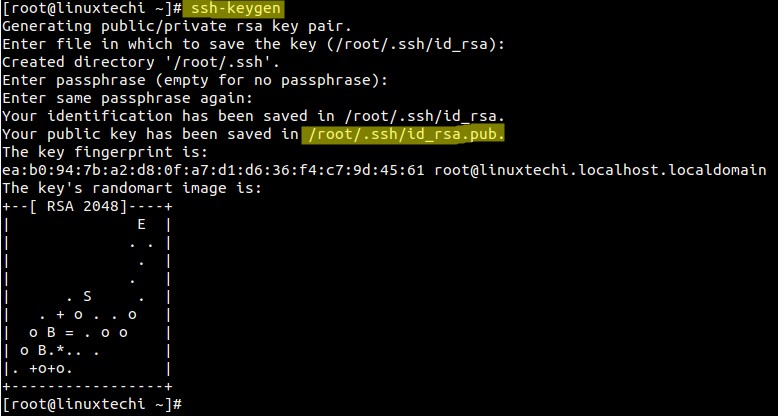
When I clone an OS image to a new, identical hardware PC I of course need to change the host name in a couple of places on the new machine. I suspect it is also good practice to generate new ssh keys for use by openssh server. May 31, 2015 Use ssh-keygen command to generate private and public key as follows. Keys are created by default in user’s.ssh folder. We can provide passphrase during creation of key but that passphrase we have to provide whenever ssh authentication happens so I kept it blank. Keys idrsa.pub is public key and idrsa is private key.
am a new RHEL 8 server sysadmin. How do I configure SSH public key-based authentication for RHEL (Red Hat Enterprise Linux) 8 server?Introduction – SSH is an acronym for secure shell. It is a suite of cryptographic network protocol. It allows users to log in and transfer files securely over the unsecure network such as the Internet. OpenSSH is an implementation of SSH protocol on RHEL 8. You can log in using RHEL 8 user and password account. However, OpenSSH project recommends log in using a combination of a private and public SSH keys.
Sample set up for our RHEL 8 server
Where,
- You generate a key pair on your Linux/Unix/macOS desktop.
- Place the public key on RHEL 8 server.
- One can unlock public key using a private key stored on your desktop with the help of ssh command.
- When both the public and private key correct you can log in without a password.
How do I set up SSH keys on RHEL 8 server?
The procedure to set up SSH key on Red Hat Enteprise Linux 8 server:
- On your local desktop type:
ssh-keygen - Install public key into remote RHEL 8 server using:
ssh-copy-id user@remote-RHEL8-server-ip - Use ssh for password less login:
ssh user@remote-RHEL8-server-ip
Let us see all commands and steps in details.
How to create the ed25519 or RSA key pair
The syntax is:ssh-keygen -t ed25519
ssh-keygen -t rsa
ssh-keygen -t rsa -b 4096 -f ~/.ssh/aws-lighsail.key -C 'My AWS SSH Keys'
ssh-keygen -t ed25519 -f ~/.ssh/linode-usa-www1-vps.key -C 'My Linode SSH Keys for www'
Where,

- -t rsa OR -t ed25519 : Specifies the type of key to create. The possible values “dsa”, “ecdsa”, “ed25519”, or “rsa” for SSH protocol version 2.
- -b 4096 : Specifies the number of bits in the key to create.
- -f~/.ssh/aws-lighsail.key : Specifies the filename of the key file.
- -C -C 'My AWS SSH Keys' : Set a new comment.
I am going type the following command on my Ubuntu desktop to create the key pair:$ ssh-keygen -t ed25519
I strongly recommend that you set up a passphrase when prompted.
How to copy the public key
Now our key paid generated and stored in ~/.ssh/ directory. You must copy a public SSH key file named ~/.ssh/id_ed25519.pub (or ~/.ssh/id_rsa.pub if you created RSA key) to the RHEL 8 server. Try the ssh-copy-id command as follows:$ ssh-copy-id -i ~/.ssh/fileNameHere.pubuser@remote-RHEL8-server-ip
For example:$ ssh-copy-id -i ~/.ssh/id_ed25519.pub [email protected]
How to log in using ssh and without a password
Now try logging into the machine, with the ssh command as follows:$ ssh user@rhel-8-server
$ ssh [email protected]
You should be able to log in without a password. If you set up a passphrase, unlock it as follows for your current session so that you don’t have to enter it every time you run ssh, sftp, scp, rsync and other commands:$ ssh-agent $SHELL
$ ssh-add
Optional settings for root user
Disable root user log in all together on RHEL 8 via ssh. Log in as root user on RHEL 8 and run following to add a user named vivek to wheel group:# usermod -aG wheel vivek
# id vivek
Allows users in group wheel can use sudo command to run all commands on RHEL 8 server. Next disable root user login by adding the following line to sshd_config:# vi /etc/ssh/sshd_config
Disable the password for root login and only allow ssh keys based login:
Save and close the file. Reload the ssh server:# systemctl reload sshd.service
For more info see “Top 20 OpenSSH Server Best Security Practices“.
Conclusion
You learned how to set up and use SSH keys to manage your RHEL 8 based server. For more info see OpenSSH man pages here.
ADVERTISEMENTS
Set up your first SSH keys
Use SSH keys for authentication when you are connecting to your server, or even between your servers. They can greatly simplify and increase the security of your login process. When keys are implemented correctly they provide a secure, fast, and easy way of accessing your cloud server.
Follow our guide and learn how to set up your first SSH keys for authentication using OpenSSH or PuTTYTray.
Preparing your server
To add an SSH key pair, first, create a hidden folder to your user account home directory on your cloud server with the following command.
Then restrict the permissions to that directory to just yourself with the command below.
This creates a secure location for you to save your SSH keys for authentication. However, note that since the keys are stored in your user home directory, every user that wishes to connect using SSH keys for authentication has to repeat these steps on their own profile.
Using OpenSSH to generate a key pair
Now continue on your own computer if you are using Linux or any other OS that has OpenSSH. PuTTY users should skip to the next section.
1. Generate a new key pair in a terminal with the next command
The key generator will ask for location and file name to which the key is saved to. Enter a new name or use the default by pressing enter.
2. (Optional) Create a passphrase for the key when prompted
This is a simple password that will protect your private key should someone be able to get their hands on it. Enter the password you wish or continue without a password. Press enter twice. Note that some automation tools might not be able to unlock passphrase-protected private keys.
3. Copy the public half of the key pair to your cloud server using the following command
Replace the user and server with your username and the server address you wish to use the key authentication on.
This also assumes you saved the key pair using the default file name and location. If not, just replace the key path ~/.ssh/id_rsa.pub above with your own key name.
Enter your user account password for that SSH server when prompted.
Proxy re encryption key generation 2017. The desired situations are: (1) Bob can decrypt mails delegated from Alice by using only his private key, (2) Bob’s mail gateway, with a trapdoor from Bob, can test whether the email delegated from Alice contains some keywords, such as “urgent”, (3) Alice and Bob do not wish to give the mail server or mail gateway the access to the content of emails.The function of proxy re-encryption with keyword search (PRES) is the combination of proxy re-encryption (PRE) and public key encryption with keyword search (PEKS).
You can now authenticate to your server with the key pair, but at the moment you would need to enter the passphrase every time you connect.
4. (Optional) Set up SSH Agent to store the keys to avoid having to re-enter passphrase at every login
Enter the following commands to start the agent and add the private SSH key.
Type in your key’s current passphrase when asked. If you saved the private key somewhere other than the default location and name, you’ll have to specify it when adding the key.
Afterwards, you can connect to your cloud server using the keys for authentication, and only having to unlock the key by repeating the last 2 steps once after every computer restart.
Using PuTTYTray to generate a key pair
If you are running Windows and PuTTYTray for SSH, you can use the built-in key generator from PuTTY to create a new key pair.
Rhel 7 Generate Ssh Host Keys Download
1. Click the Keygen button at the bottom of the PuTTY Configuration window to get started.
Then in the Key Generator window, check that the Type of key to generate at the bottom is set to SSH-2 RSA. The older SSH-1 was the first version on the standard but is now generally considered obsolete. Most modern servers and clients support SSH-2.
2. Click the Generate button to begin.
3. Keep moving your mouse over the blank area in any manner to help generate randomness for a few moments until the progress is complete.
With the keys finished, PuTTY will show the relative information about the pair along with the public key for easier copying.
4. (Optional) Enter a key passphrase in the 2 empty fields for the added security before continuing. The passphrase will protect your key from unauthorized use should someone be able to copy it. However, some automation tools might not be able to unlock passphrase-protected private keys.
5. Click the Save private key button and store it somewhere safe. Generally anywhere in your user directory is fine as long as your PC is password protected. Before closing the keygen, you may want to copy the public key to your clipboard, but you can always get it later as well.
Now that you have a new key saved on your computer, you’ll need to import it into the PuTTY key agent.
6. Click the Agent button to open the key manager in the PuTTY Configuration window.
7. Click Add Key button in the Key List, then browse to the location you saved the private key, select it and click Open.
Enter your key passphrase if asked.
This will import the key to your PuTTY client, but you still need to copy the public key over to your server.
8. Open an SSH connection to your cloud server and go to the SSH key directory.
9. Open or create the default file OpenSSH looks for public keys called authorized_keys.
10. Paste the public key into the file by simply right-clicking the SSH client window. Make sure the key goes on a single line for OpenSSH to be able to read it.
When you’ve copied the public key over to the authorized keys list, save the file and exit the editor. You can now test the public key authentication by logging in to your server again. You should not get asked for your password, but instead logged straight in with the key. If it’s not working, check that your private key is unlocked at your SSH Agent and try again.
Turn off password authentication
With SSH key authentication configured and tested, you can disable password authentication for SSH all together to prevent brute-forcing. Generate ssl key and cert linux. When logged in to your cloud server.
1. Open the SSH configuration file with the following command.
2. Set the password authentication to no to disable clear text passwords.
3. Check that public key authentication is enabled, just to be safe and not get locked out from your server. If you do find yourself unable to log in with SSH, you can always use the Web terminal at your UpCloud control panel.
Rhel 7 Generate Ssh Host Keys Code
Then save and exit the editor.
Rhel 7 Generate Ssh Host Keys Free
4. Restart the SSH service to apply the changes by using the command below.
With that done your cloud server is now another step along towards security. Malicious attempts to connect to your server will results in authentication rejection, as plain passwords are not allowed, and brute-forcing an RSA key is practically impossible.
Conclusions
Remember to always keep your private keys safe. You can use the same key from multiple computers if you wish, or generate new ones on each client connecting to your cloud server for added security. Each user should generate their own key pair and passphrase for secure access control. With proper management, even in case one of the private keys gets compromised you won’t have to replace them all.